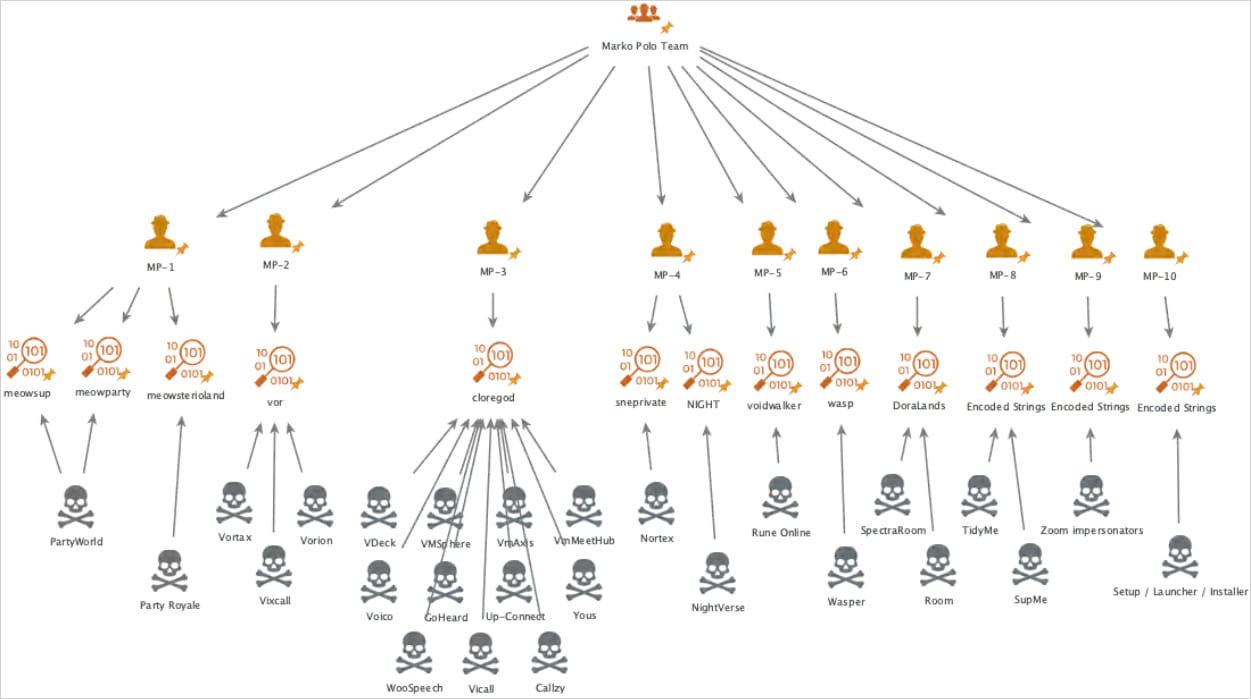
A large infostealer malware operation encompassing thirty campaigns concentrating on a broad spectrum of demographics and system platforms has been uncovered, attributed to a cybercriminal group named “Marko Polo.”
The menace actors use quite a lot of distribution channels, together with malvertising, spearphishing, and model impersonation in on-line gaming, cryptocurrency, and software program, to unfold 50 malware payloads, together with AMOS, Stealc, and Rhadamanthys.
In keeping with Recorded Future’s Insikt Group, which has been monitoring the Marko Polo operation, the malware marketing campaign has impacted 1000’s, with potential monetary losses within the hundreds of thousands.
“Based on the widespread nature of the Marko Polo campaign, Insikt Group suspects that likely tens of thousands of devices have been compromised globally — exposing sensitive personal and corporate data,” warns Recorded Future’s Insikt Group.
“This poses significant risks to both consumer privacy and business continuity. Almost certainly generating millions of dollars in illicit revenue, this operation also highlights the negative economic effects of such cybercriminal activities.”
Supply: Recorded Future
Setting high-value traps
Insikt Group experiences that Marko Polo primarily depends on spearphishing through direct messages on social media platforms to achieve high-value targets comparable to cryptocurrency influencers, players, software program builders, and different folks more likely to deal with precious information or belongings.
Victims are lured into downloading malicious software program by interacting with what they’re tricked into believing are authentic job alternatives or mission collaborations.
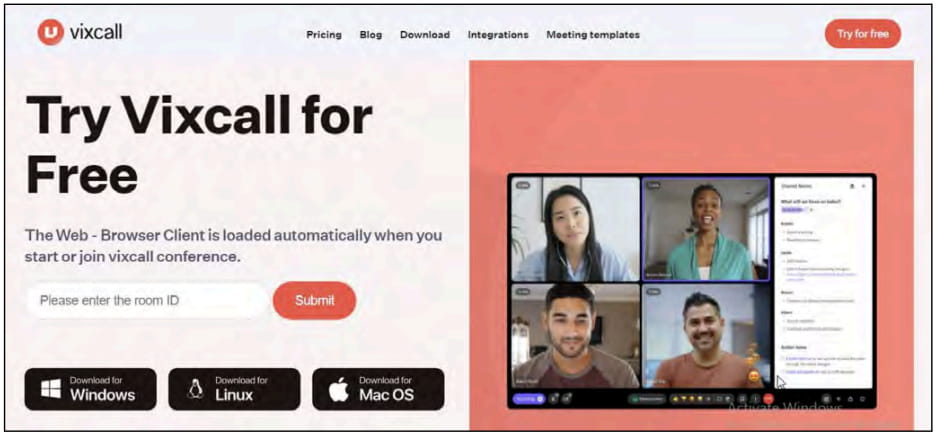
A few of the manufacturers which are impersonated embody Fortnite (gaming), Get together Icon (gaming), RuneScape (gaming), Rise On-line World (gaming), Zoom (productiveness), and PeerMe (cryptocurrency).
Marko Polo additionally makes use of its personal made-up manufacturers not associated to present tasks, like Vortax/Vorion and VDeck (assembly software program), Wasper and PDFUnity (collaboration platforms), SpectraRoom (crypto communications), and NightVerse (web3 recreation).
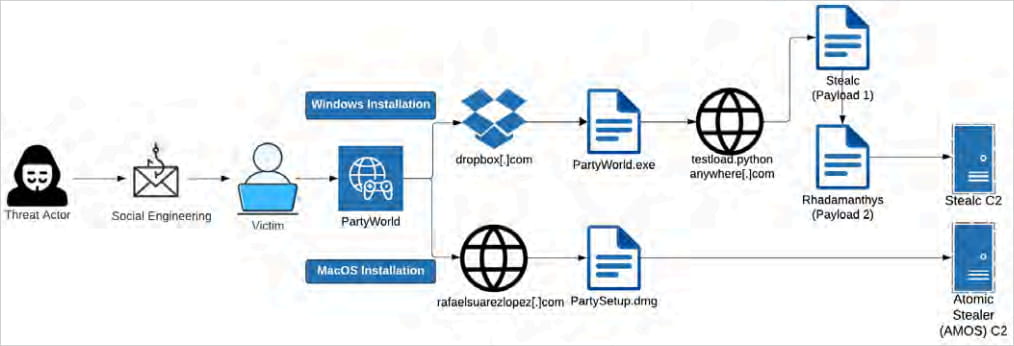
In some instances, the victims are led to a web site for faux digital assembly, messaging, and recreation purposes, that are used to put in malware. Different campaigns distribute the malware by means of executables (.exe or .dmg) in torrent information.
Supply: Recorded Future
Hitting each Home windows and macOS
Marko Polo’s toolkit is numerous, displaying the menace group’s functionality to hold out multi-platform and multi-vector assaults.
On Home windows, HijackLoader is used for delivering Stealc, a general-purpose light-weight info-stealer designed to gather information from browsers and crypto pockets apps, or Rhadamanthys, a extra specialised stealer that targets a broad vary of purposes and information sorts.
In a latest replace, Rhadamanthys added a clipper plugin able to diverting cryptocurrency funds to the attackers’ wallets, the flexibility to get better deleted Google Account cookies, and Home windows Defender evasion.
When the goal makes use of macOS, Marko Polo deploys Atomic (‘AMOS’). This stealer launched in mid-2023, rented to cybercriminals for $1,000/month, permitting them to grab numerous information saved in internet browsers.
AMOS also can brute-force MetaMask seeds and steal Apple Keychain passwords to pay money for WiFi passwords, saved logins, bank card information, and different encrypted info saved on macOS.
Supply: Recorded Future
Malicious campaigns involving information-stealing malware have seen large development through the years, with menace actors concentrating on victims by means of zero-day vulnerabilities, faux VPNs, fixes to GitHub points, and even solutions on StackOverflow.
These credentials are then used to breach company networks, conduct information theft campaigns like we noticed with the huge SnowFlake account breaches, and trigger chaos by corrupting community routing info.
To mitigate the chance of downloading and operating infostealer malware in your system, don’t observe hyperlinks shared by strangers and solely obtain software program from the official mission web sites.
The malware utilized by Marko Polo is detected by newest antivirus software program, so scanning downloaded information earlier than executing them ought to disrupt the an infection course of earlier than it begins.
