Cyberattackers and hacktivists are more and more focusing on the United Arab Emirates, the Kingdom of Saudi Arabia, and different nations within the Gulf Cooperative Council (GCC) area. The area is probably going a well-liked goal as a result of it is a hub for commerce and commerce, filled with wealthy economies; and due to regional nations’ stance on sure geopolitical points.
That is in keeping with 18 months of Darkish Net information compiled by Moscow-based risk analysis agency Constructive Applied sciences. The report said that the primary half of the 12 months, the variety of distributed denial-of-service (DDoS) assaults within the area rose 70%, in contrast with the identical interval within the earlier 12 months.
Hacktivists use boards as each a strategy to name like-minded hackers to motion and to publish proof of their success in opposition to particular targets, says Anastasiya Chursina, a risk analyst with Constructive Applied sciences.
“We believe that this trend may continue and the number of attacks carried out by hacktivists will go up,” she says. “At the same time, the level of other attacks will increase, which will entail an increase in the number of risks and negative consequences for companies in the region.”
Each Saudi Arabia and the UAE topped the chart of focused nations in a March evaluation of two years of assaults within the area. The UAE alone faces a mean of fifty,000 cyberattacks day-after-day, the top of cybersecurity for the UAE authorities stated earlier this 12 months, whereas the nation additionally has a quickly rising assault floor.
Extra assaults are additionally being publicly disclosed: In July, pro-Palestinian hacktivist group BlackMeta focused a financial institution within the United Arab Emirates with a DoS marketing campaign that lasted greater than 100 hours over six days. And in April, Saudi Arabia was added to the record of organizations focused by the suspected China-linked group Photo voltaic Spider.
Extra Cyber Risk Actors Coming On-line?
The rise of DoS assaults — relatively than Net defacements or system breaches — could point out an inflow of recent risk actors. The attackers’ ways of selection rely on their abilities and information, and DDoS assaults will be completed by novice hackers, says Constructive Applied sciences’ Chursina.
“The main goal of hacktivists is to draw public attention to certain political, social, and religious issues,” she says. “DDoS attacks are the most popular, as they do not require high professional knowledge and resources, and they can be performed by any novice hacker.”
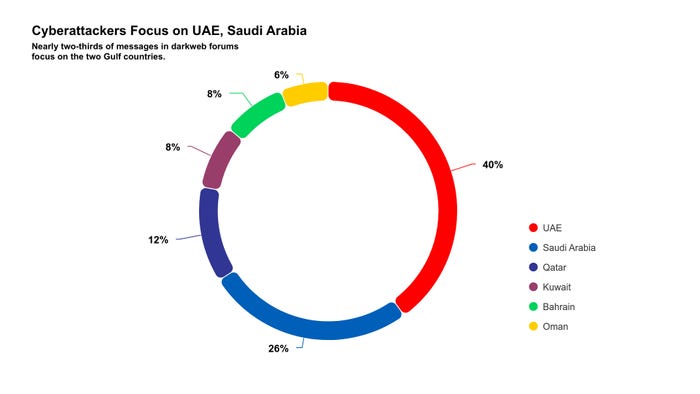
Constructive Applied sciences’ trove of discussion board posts and textual content messages totals 277 million gadgets from 380 Telegram channels and Darkish Net boards. For its GCC report, the corporate centered on six main nations within the area: the UAE, Saudi Arabia, Bahrain, Oman, Qatar, and Kuwait.
Stolen information and illicit entry accounted for the subject of greater than half (54%) of the posts, with the overwhelming majority of of customers promoting or shopping for entry. These posts centered on 5 sectors: commerce, providers, manufacturing, IT, and authorities companies.
About 12% of the posts included a name to motion for hacktivism or proof of a profitable hacktivist assault, in keeping with the report. About 9% of hacktivist posts additionally marketed free credentials to be used in assaults.
“Access giveaways represent a new trend for the region that first appeared in H2 2023,” the report said. “Most access giveaways (70%) contained the credentials of government agency employees.”
Cyber Area Favored for Assaults, Espionage
Cyberattacks have develop into the popular battlefield for a lot of teams — each nation-state and dissent organizations — within the area. The stakes are quickly escalating as properly, from Iran’s rising tempo of cyber espionage to Israel’s cyber-physical assaults utilizing compromised provide chains to the compromise of naval data methods within the area.
With the UAE and Saudi Arabia more and more invested in digitization, AI improvement, and shifting to a knowledge-based financial system, organizations within the two nations — and the Center East at giant — have to concentrate on strengthening their cybersecurity posture, Constructive Applied sciences says.
“Dark Web forums are full of offers and services tailored to this region,” the corporate’s report said. “The abundance of posts related to the sale of access, often low-cost, makes it easier for attackers to gain initial access to a company and carry out an attack without wasting time looking for new entry points into the infrastructure. Access giveaways are a new trend on the part of haсktivists allowing low-grade hackers to carry out attacks and raise public awareness about social and political issues.”