Telegram mounted a zero-day vulnerability in its Home windows desktop utility that could possibly be used to bypass safety warnings and routinely launch Python scripts.
Over the previous few days, rumors have been circulating on X and hacking boards about an alleged distant code execution vulnerability in Telegram for Home windows.
Whereas a few of these posts claimed it was a zero-click flaw, the movies demonstrating the alleged safety warning bypass and RCE vulnerability clearly present somebody clicking on shared media to launch the Home windows calculator.
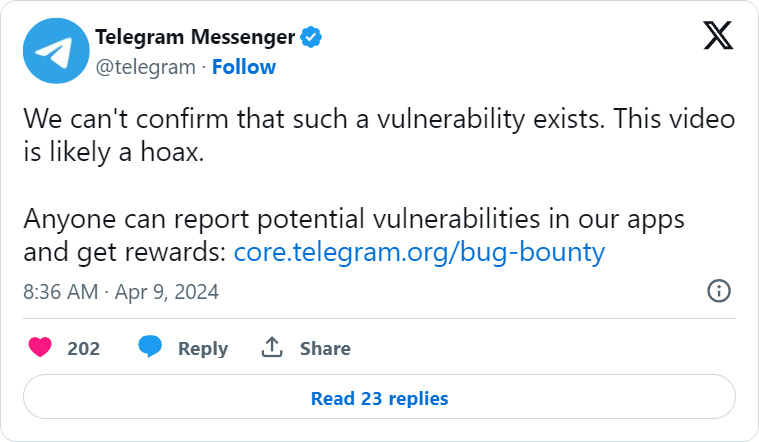
Telegram shortly disputed these claims, stating that they “can’t confirm that such a vulnerability exists” and that the video is probably going a hoax.
Nevertheless, the subsequent day, a proof of idea exploit was shared on the XSS hacking discussion board explaining {that a} typo within the supply code for Telegram for Home windows could possibly be exploited to ship Python .pyzw information that bypass safety warnings when clicked.
This triggered the file to routinely be executed by Python with no warning from Telegram prefer it does for different executables, and was speculated to do for this file if it wasn’t for a typo.
To make issues worse, the proof of idea exploit disguised the Python file as a shared video, together with a thumbnail, that could possibly be used to trick customers into clicking on the faux video to look at it.
In an announcement to BleepingComputer, Telegram rightfully disputes that the bug was a zero-click flaw however confirmed they mounted the “issue” in Telegram for Home windows to stop Python scripts from routinely launching when clicked. This was a server-side repair, which we clarify within the subsequent part
“Rumors about the existence of zero-click vulnerabilities in Telegram Desktop are inaccurate. Some “specialists” recommended to “disable computerized downloads” on Telegram — there have been no points which may have been triggered by computerized downloads.
Nevertheless, on Telegram Desktop, there was a difficulty that required the consumer to CLICK on a malicious file whereas having the Python interpreter put in on their pc. Opposite to earlier reviews, this was not a zero-click vulnerability and it may have an effect on solely a tiny fraction of our consumer base: lower than 0.01% of our customers have Python put in and use the related model of Telegram for Desktop.
A server-side repair has been utilized to make sure that even this situation now not reproduces, so all variations of Telegram Desktop (together with all older ones) now not have this situation.”
❖ Telegram
BleepingComputer requested Telegram how they know what software program is put in on consumer’s Home windows gadgets, as this kind of information will not be talked about of their Privateness Coverage.
The Telegram vulnerability
The Telegram Desktop shopper retains observe of a checklist of file extensions related to dangerous information, akin to executable information.
When somebody sends considered one of these file sorts in Telegram, and a consumer clicks on the file, as an alternative of routinely launching within the related program in Home windows, Telegram first shows the next safety warning.
“This file has the extension .exe. It may harm your computer. Are you sure you want to run it?,” reads the Telegram warning.
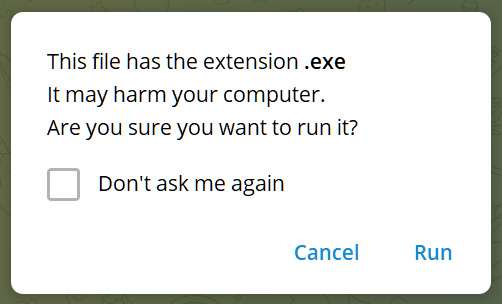
Supply: BleepingComputer
Nevertheless, unknown file sorts shared in Telegram will routinely be launched in Home windows, letting the working system determine what program to make use of.
When Python for Home windows is put in, it can affiliate the .pyzw file extension with the Python executable, inflicting Python to execute the scripts routinely when the file is double-clicked.
The .pyzw extension is for Python zipapps, that are self-contained Python applications contained inside ZIP archives.
The Telegram builders have been conscious that a majority of these executables ought to be thought-about dangerous and added it to the checklist of executable file extensions.
Sadly, after they added the extension, they made a typo, getting into the extension as ‘pywz‘ quite than the right spelling of ‘pyzw‘.
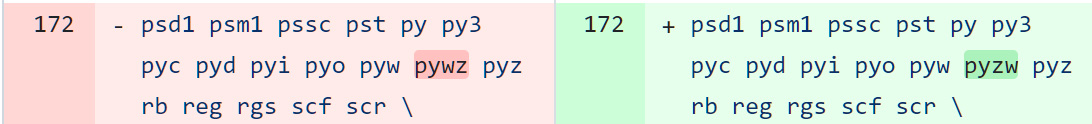
Supply: BleepingComputer.com
Due to this fact, when these information have been despatched over Telegram and clicked on, they have been routinely launched by Python if it was put in in Home windows.
This successfully permits attackers to bypass safety warnings and remotely execute code on a goal’s Home windows system if they’ll trick them into opening the file.
To masquerade the file, researchers devised utilizing a Telegram bot to ship the file with a mime kind of ‘video/mp4,’ inflicting Telegram to show the file as a shared video.
If a consumer clicks on the video to look at it, the script will routinely be launched by way of Python for Home windows.
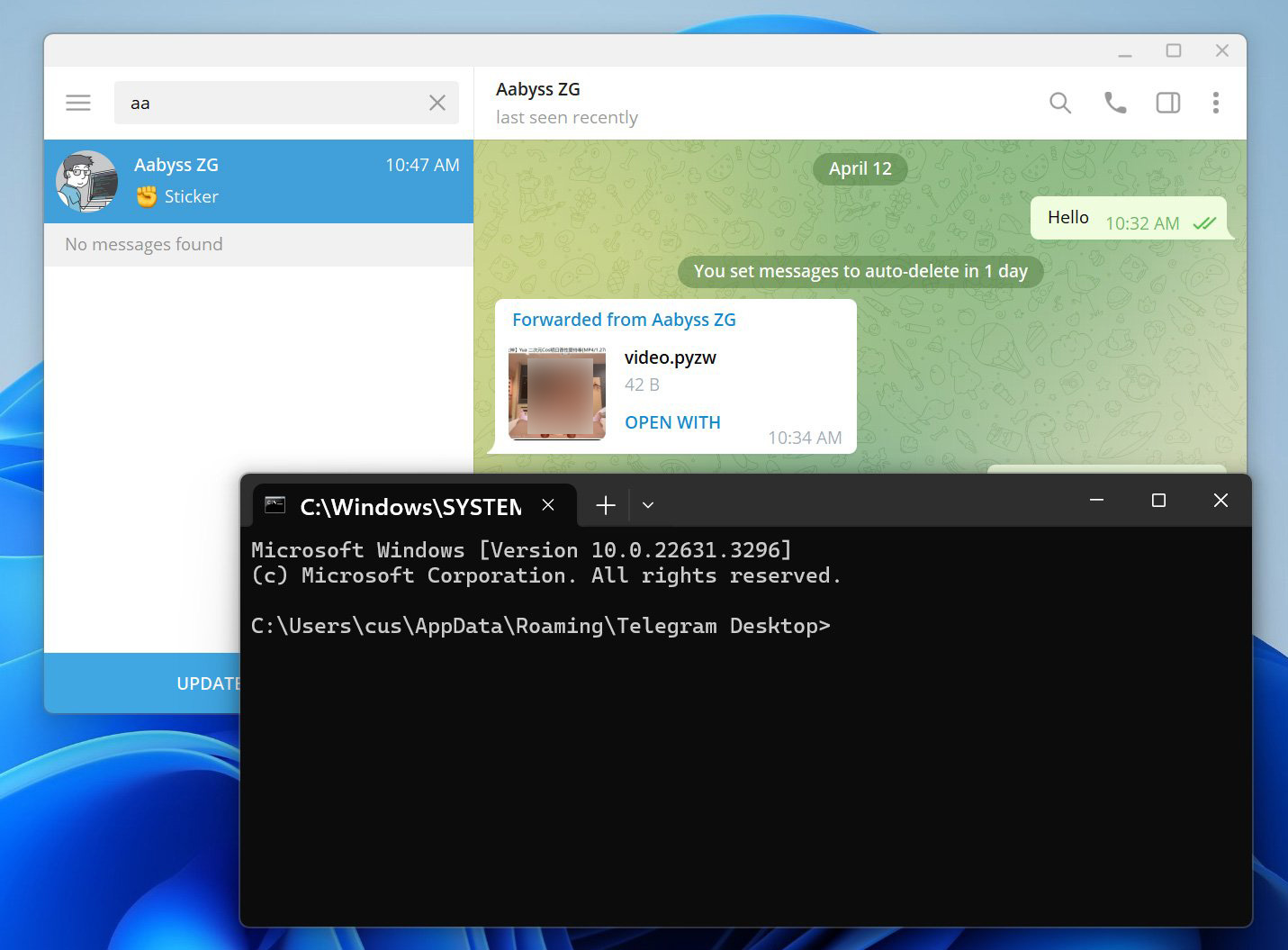
BleepingComputer examined this exploit with cybersecurity researcher AabyssZG, who additionally shared demonstrations on X.
Utilizing an older model of Telegram, BleepingComputer obtained ‘video.pywz’ file from the researcher disguised as a mp4 video. This file merely comprises Python code to open a command immediate, as proven under.
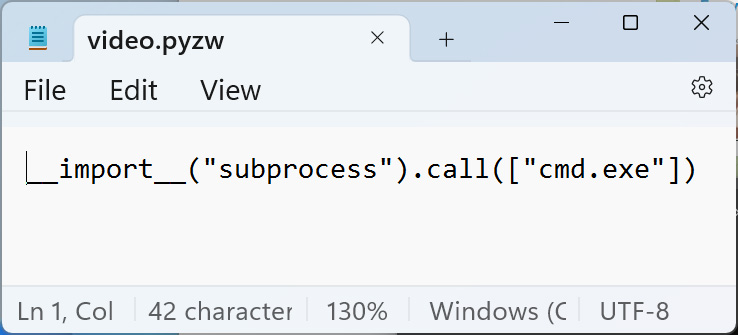
Supply: BleepingComputer
Nevertheless, as you possibly can see under, while you click on on the video to look at it, Python routinely executes the script, which opens the command immediate. Observe that we redacted the video thumbnail because it’s barely NSFW.
Supply: BleepingComputer
The bug was reported to Telegram on April tenth, they usually mounted it by correcting the extension spelling within the ‘data_document_resolver.cpp’ supply code file.
Nevertheless, this repair doesn’t look like stay as of but, because the warnings don’t seem while you click on on the file to launch it.
As a substitute, Telegram utilized a server-side repair that appends the .untrusted extension to pyzq information, that when clicked, will trigger Home windows to ask what program you want to use to open it, quite than routinely launching in Python.
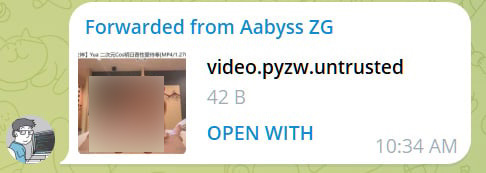
Supply: BleepingComputer
Future variations of the Telegram Desktop app ought to embrace the safety warning message quite than appending the “.untrusted” extension, including a bit extra safety to the method.
