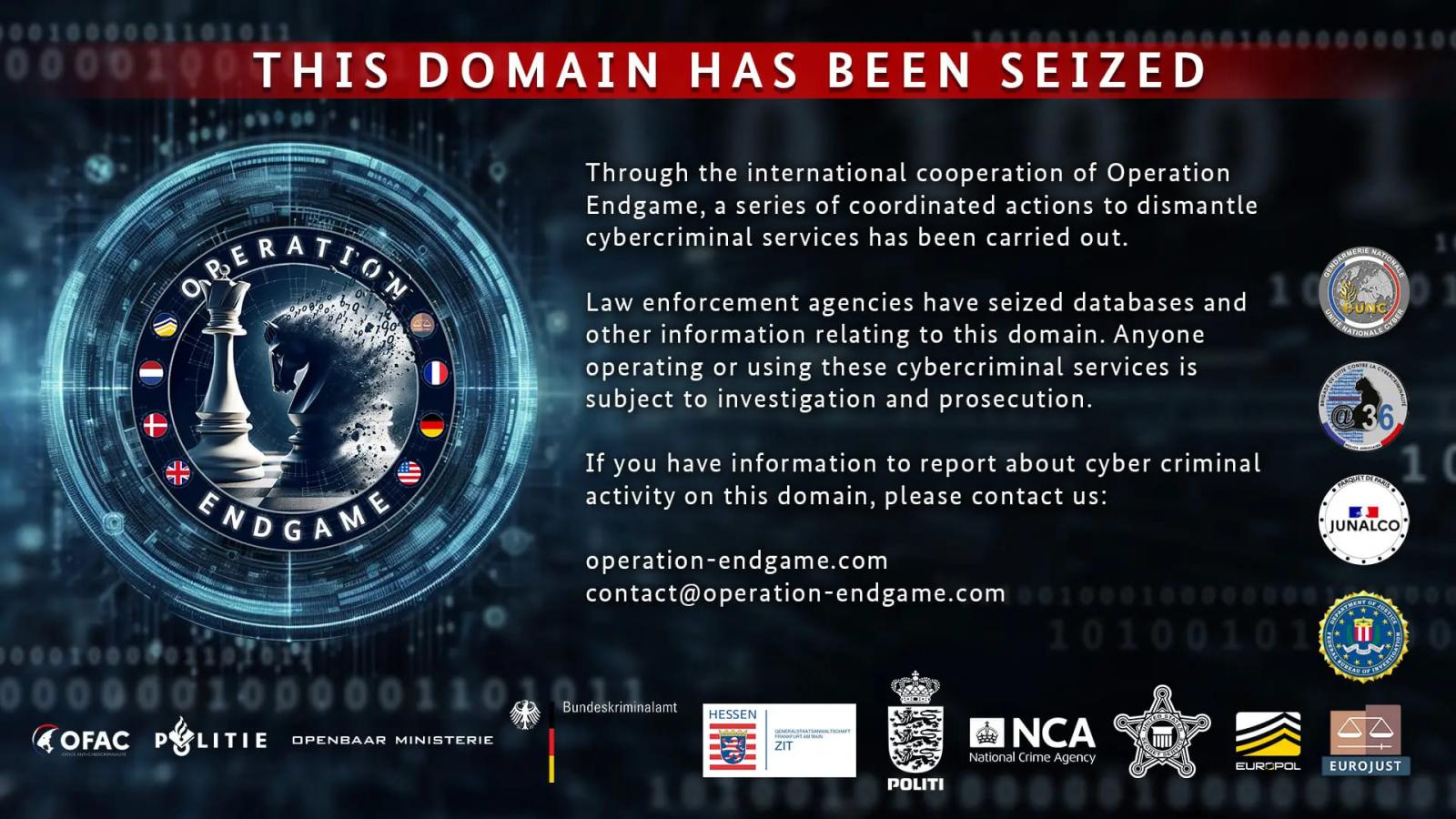
A world legislation enforcement operation codenamed ‘Operation Endgame’ has seized over 100 servers worldwide utilized by a number of main malware loader operations, together with IcedID, Pikabot, Trickbot, Bumblebee, Smokeloader, and SystemBC.
The motion, which occurred between Might 27 and 29, 2024, concerned 16 location searches throughout Europe and led to the arrest of 4 people, one in Armenia and three in Ukraine.
Moreover, the police have recognized eight fugitives linked to the malware operations, who will probably be added to Europol’s ‘Most Wanted’ listing later right this moment.
The seized infrastructure was unfold throughout Europe and North America, internet hosting over 2,000 domains that facilitated illicit companies, all beneath the management of the authorities now.
Operation Endgame concerned police forces from Germany, the US, the UK, France, Denmark, and the Netherlands.
The operation was supported by intelligence supplied by consultants from Bitdefender, Cryptolaemus, Sekoia, Shadowserver, Group Cymru, Prodaft, Proofpoint, NFIR, Computest, Northwave, Fox-IT, HaveIBeenPwned, Spamhaus, and DIVD.
Tens of millions of computer systems contaminated
Malware droppers are specialised instruments designed to ascertain preliminary entry to units. The cybercriminals behind them usually ship malicious emails to ship the malware or cover payloads on trojanized installers promoted by means of malvertising or torrents.
Many of those droppers began as banking trojans and later developed to give attention to preliminary entry, whereas additionally simplifying their operation and stripping out malicious options to cut back the chance of detection.
They make use of evasive ways akin to heavy code obfuscation and bonafide course of impersonation, typically residing in reminiscence.
As soon as the an infection is established, they introduce extra harmful payloads to the compromised system, akin to info stealers and ransomware.
Europol stated that one of many fundamental suspects concerned in one of many focused malware operations remodeled 69 million Euros ($74.5M) by renting out their infrastructure for ransomware deployment.
“It has been discovered through the investigations so far that one of the main suspects has earned at least EUR 69 million in cryptocurrency by renting out criminal infrastructure sites to deploy ransomware,” reads Europol’s announcement.
“The suspect’s transactions are constantly being monitored and legal permission to seize these assets upon future actions has already been obtained.”
Extra details about the suspects and the legislation enforcement operation is scheduled to be printed on this devoted portal later right this moment.
