A researcher has launched a device to bypass Google’s new App-Certain encryption cookie-theft defenses and extract saved credentials from the Chrome internet browser.
The device, named ‘Chrome-App-Certain-Encryption-Decryption,’ was launched by cybersecurity researcher Alexander Hagenah after he observed that others had been already determining comparable bypasses.
Though the device achieves what a number of infostealer operations have already added to their malware, its public availability raises the chance for Chrome customers who proceed to retailer delicate knowledge of their browsers.
Google’s app-bound encryption issues
Google launched Software-Certain (App-Certain) encryption in July (Chrome 127) as a brand new safety mechanism that encrypts cookies utilizing a Home windows service that runs with SYSTEM privileges.
The purpose was to guard delicate data from infostealer malware, which runs with the permissions of the logged person, making it inconceivable for it to decrypt stolen cookies with out first gaining SYSTEM privileges and doubtlessly elevating alarms in safety software program.
“Because the App-Bound service is running with system privileges, attackers need to do more than just coax a user into running a malicious app,” defined Google in July.
“Now, the malware has to gain system privileges, or inject code into Chrome, something that legitimate software shouldn’t be doing.”
Nonetheless, by September, a number of data stealers had discovered methods to bypass the brand new safety characteristic and supply their cybercriminal prospects the power to as soon as once more steal and decrypt delicate data from Google Chrome.
Google informed BleepingComputer then that the “cat and mouse” sport between info-stealer builders and its engineers was all the time anticipated and that they by no means assumed that their protection mechanisms could be bulletproof.
As a substitute, with the introduction of App-Certain encryption, they hoped they might lastly lay the bottom for regularly constructing a extra sound system. Under is Google’s response from the time:
“We’re conscious of the disruption that this new protection has brought on to the infostealer panorama and, as we acknowledged within the weblog, we count on this safety to trigger a shift in attacker conduct to extra observable strategies akin to injection or reminiscence scraping. This matches the brand new conduct we have now seen.
We proceed to work with OS and AV distributors to attempt to extra reliably detect these new sorts of assaults, in addition to persevering with to iterate on hardening defenses to enhance safety in opposition to infostealers for our customers.” – A Google spokesperson
Bypass now publicly out there
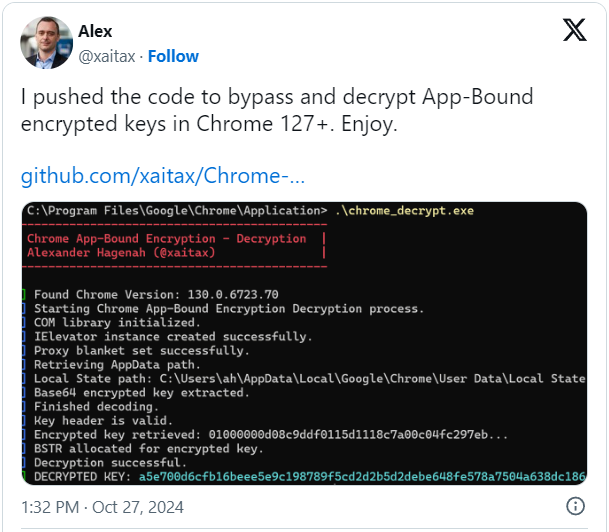
Yesterday, Hagenah made his App-Certain encryption bypass device out there on GitHub, sharing supply code that permits anybody to study from and compile the device.
“This tool decrypts App-Bound encrypted keys stored in Chrome’s Local State file, using Chrome’s internal COM-based IElevator service,” reads the challenge description.
“The tool provides a way to retrieve and decrypt these keys, which Chrome protects via App-Bound Encryption (ABE) to prevent unauthorized access to secure data like cookies (and potentially passwords and payment information in the future).”
To make use of the device, customers should copy the executable into the Google Chrome listing often positioned at C:Program FilesGoogleChromeApplication. This folder is protected, so customers should first achieve administrator privileges to repeat the executable to that folder.
Nonetheless, that is generally straightforward to realize as many Home windows customers, particularly customers, use accounts which have administrative privileges.
When it comes to its precise impression on Chrome safety, researcher g0njxa informed BleepingComputer that Hagenah’s device demonstrates a primary methodology that the majority infostealers have now surpassed to steal cookies from all variations of Google Chrome.
eSentire malware analyst Russian Panda additionally confirmed to BleepingComputer that Hagenah’s methodology seems to be much like the early bypassing approaches infostealers took when Google first applied App-Certain encryption in Chrome.
“Lumma used this method – instantiating the Chrome IElevator interface through COM to access Chrome’s Elevation Service to decrypt the cookies, but this can be quite noisy and easy to detect,” Russian Panda informed BleepingComputer.
“Now, they are using indirect decryption without directly interacting with Chrome’s Elevation Service”.
Nonetheless, g0njxa commented that Google has nonetheless not caught up, so person secrets and techniques saved in Chrome may be simply stolen utilizing the brand new device.
In response to the discharge of this device, Google shared the next assertion with BleepingComputer:
“This code [xaitax’s] requires admin privileges, which shows that we’ve successfully elevated the amount of access required to successfully pull off this type of attack,” Google informed BleepingComputer.
Whereas it’s true admin privileges are required, it doesn’t appear to have impacted information-stealing malware operations, which have solely elevated over the previous six months, focusing on customers by means of zero-day vulnerabilities, faux fixes to GitHub points, and even solutions on StackOverflow.