Hackers have used new GodLoader malware exploiting the capabilities of the broadly used Godot sport engine to evade detection and infect over 17,000 methods in simply three months.
As Test Level Analysis discovered whereas investigating the assaults, risk actors can use this malware loader to focus on players throughout all main platforms, together with Home windows, macOS, Linux, Android, and iOS.
It is also used to leverage Godot’s flexibility and its GDScript scripting language capabilities to execute arbitrary code and bypass detection methods utilizing the sport engine .pck recordsdata, which bundle sport property, to embed dangerous scripts.
As soon as loaded, the maliciously crafted recordsdata set off malicious code on the victims’ units, enabling attackers to steal credentials or obtain further payloads, together with the XMRig crypto miner. This miner malware’s configuration was hosted on a personal Pastebin file uploaded in Could, which was visited 206,913 instances all through the marketing campaign.
“Since at least June 29, 2024, cybercriminals have been taking advantage of Godot Engine to execute crafted GDScript code which triggers malicious commands and delivers malware. This technique has remained undetected by most antivirus tools on VirusTotal, possibly infecting more than 17,000 machines in just a few months,” in response to Test Level.
“Godot has a vibrant and growing community of developers who value its open-source nature and powerful capabilities. Over 2,700 developers contributed to the Godot gaming engine,” whereas “on platforms like Discord, YouTube, and other social media platforms, the Godot engine has around 80,000 followers who stay updated on the latest news.”
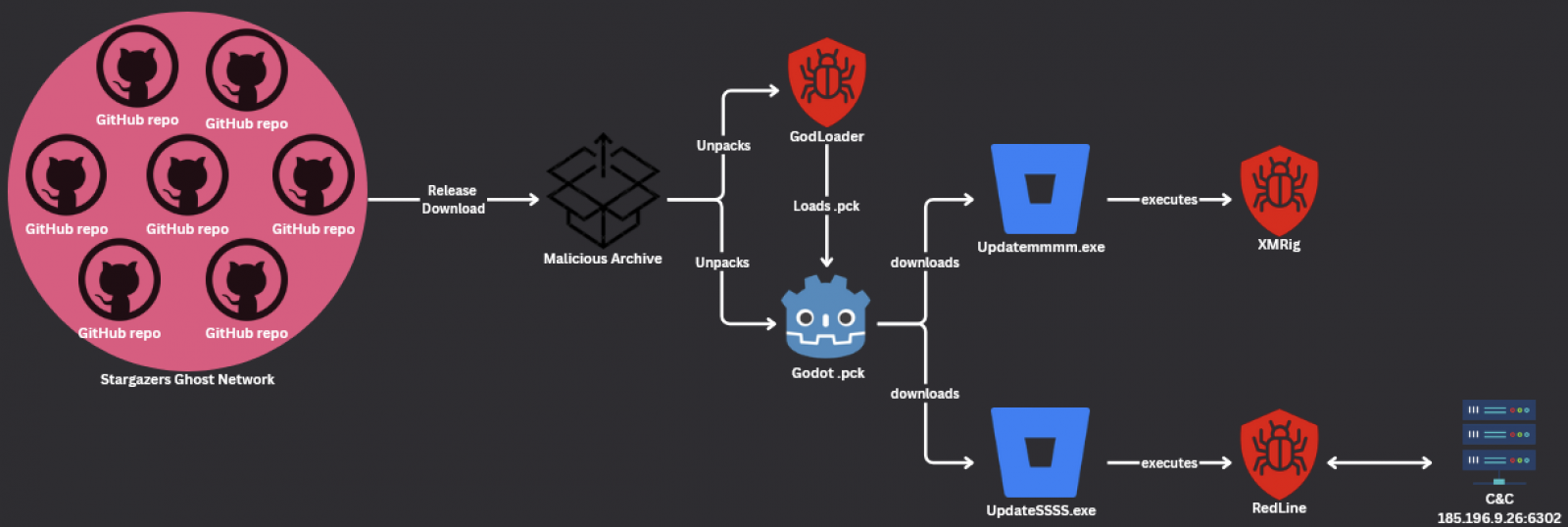
The attackers delivered the GodLoader malware via the Stargazers Ghost Community, a malware Distribution-as-a-Service (DaaS) that masks its actions utilizing seemingly respectable GitHub repositories.
Between September and October 2024, they used over 200 repositories managed by over 225 Stargazer Ghost accounts to deploy the malware to targets’ methods, exploiting potential victims’ belief in open-source platforms and seemingly respectable software program repositories.
All through the marketing campaign, Test Level detected 4 separate assault waves towards builders and players between September 12 and October 3, attractive them to obtain contaminated instruments and video games.
Whereas the safety researchers solely found GodLoader samples concentrating on Home windows methods, additionally they developed GDScript proof-of-concept exploit code displaying how simply the malware may be tailored to assault Linux and macOS methods.
Stargazer Goblin, the risk actor behind the Stargazers Ghost Community DaaS platform utilized in these assaults, was first noticed by Test Level selling this malware distribution service on the darkish internet in June 2023. Nonetheless, it has probably been lively since not less than August 2022, incomes over $100,000 since this service was launched.
The Stargazers Ghost Community makes use of over 3,000 GitHub “ghost” accounts to create networks of a whole bunch of repositories that can be utilized to ship malware (primarily data stealers like RedLine, Lumma Stealer, Rhadamanthys, RisePro, and Atlantida Stealer) and star, fork, and subscribe to those malicious repos to push them to GitHub’s trending part and enhance their obvious legitimacy.