A brand new malware marketing campaign has been exploiting the updating mechanism of the eScan antivirus software program to distribute backdoors and cryptocurrency miners like XMRig by a long-standing menace codenamed GuptiMiner focusing on giant company networks.
Cybersecurity agency Avast stated the exercise is the work of a menace actor with doable connections to a North Korean hacking group dubbed Kimsuky, which is also referred to as Black Banshee, Emerald Sleet, and TA427.
“GuptiMiner is a highly sophisticated threat that uses an interesting infection chain along with a couple of techniques that include performing DNS requests to the attacker’s DNS servers, performing sideloading, extracting payloads from innocent-looking images, signing its payloads with a custom trusted root anchor certification authority, among others,” Avast stated.
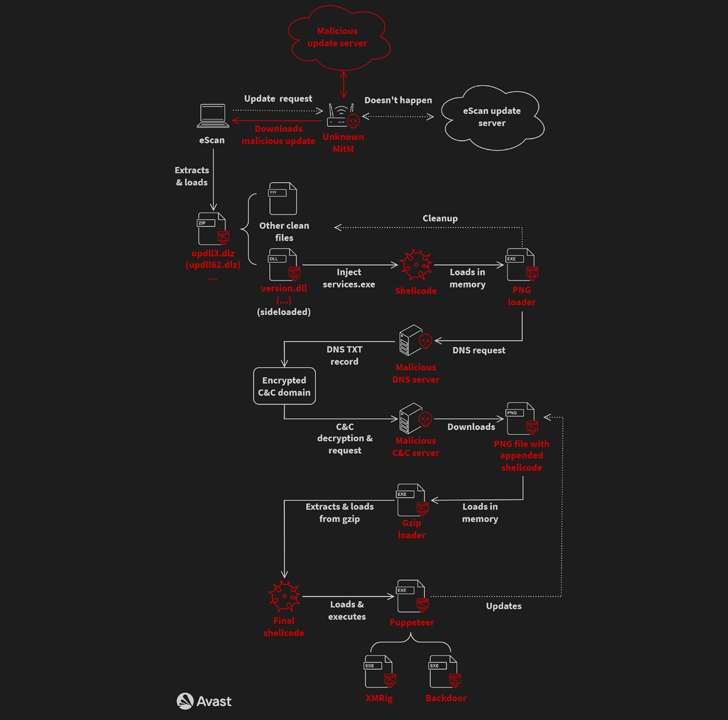
The intricate and elaborate an infection chain, at its core, leverages a safety shortcoming within the replace mechanism of Indian antivirus vendor eScan to propagate the malware via an adversary-in-the-middle (AitM) assault.
Particularly, it entails hijacking the updates by substituting the bundle file with a malicious model by benefiting from the truth that the downloads weren’t signed and secured utilizing HTTPS. The problem, which went unnoticed for at the very least 5 years, has been rectified as of July 31, 2023.
The rogue DLL (“updll62.dlz”) executed by the eScan software program side-loads a DLL (“version.dll”) to activate a multi-stage sequence beginning with a PNG file loader that, in flip, employs malicious DNS servers to contact a command-and-control (C2) server and fetch a PNG file with appended shellcode.
“GuptiMiner hosts their own DNS servers for serving true destination domain addresses of C&C servers via DNS TXT responses,” researchers Jan Rubín and Milánek stated.
“As the malware connects to the malicious DNS servers directly, the DNS protocol is completely separated from the DNS network. Thus, no legitimate DNS server will ever see the traffic from this malware.”
The PNG file is then parsed to extract the shellcode, which is then chargeable for executing a Gzip loader that is designed to decompress one other shellcode utilizing Gzip and execute it in a separate thread.
The third-stage malware, dubbed Puppeteer, pulls all of the strings, in the end deploying the XMRig cryptocurrency miner and backdoors on the contaminated programs.
Avast stated it encountered two several types of backdoors that come fitted with options to allow lateral motion, settle for instructions from the menace actor, and ship extra elements as required.
“The first is an enhanced build of PuTTY Link, providing SMB scanning of the local network and enabling lateral movement over the network to potentially vulnerable Windows 7 and Windows Server 2008 systems on the network,” the researchers defined.
“The second backdoor is multi-modular, accepting commands from the attacker to install more modules as well as focusing on scanning for stored private keys and crypto wallets on the local system.”
The deployment of XMRig has been described as “unexpected” for what’s in any other case a posh and meticulously executed operation, elevating the likelihood that the miner acts as a distraction to forestall victims from discovering the true extent of the compromise.
GuptiMiner, recognized to be lively since at the very least 2018, additionally makes use of assorted methods like anti-VM and anti-debug tips, code virtualization, dropping the PNG loader throughout system shutdown occasions, storing payloads in Home windows Registry, and including a root certificates to Home windows’ certificates retailer to make the PNG loader DLLs seem reliable.
The hyperlinks to Kimusky come from an info stealer that, whereas not distributed by GuptiMiner or through the an infection movement, has been used “across the whole GuptiMiner campaign” and shares overlaps with a keylogger beforehand recognized as utilized by the group.
It is at the moment not clear who the targets of the marketing campaign are, however GuptiMiner artifacts have been uploaded to VirusTotal from India and Germany as early as April 2018, with Avast telemetry information highlighting new infections possible originating from out-of-date eScan shoppers.
The findings come because the Korean Nationwide Police Company (KNPA) known as out North Korean hacking crews resembling Lazarus, Andariel, and Kimsuky for focusing on the protection sector within the nation and exfiltrating helpful information from a few of them.
A report from the Korea Financial Every day stated the menace actors penetrated the networks of 83 South Korean protection contractors and stole confidential info from about 10 of them from October 2022 to July 2023.