The U.S. Cybersecurity & Infrastructure Safety Company (CISA) has added three safety vulnerabilities to its ‘Recognized Exploited Vulnerabilities’ catalog, one impacting Google Chrome and two affecting some D-Hyperlink routers.
Including the problems to the KEV catalog serves as a warning to federal companies and corporations that menace actors are leveraging them in assaults and safety updates or mitigations ought to be utilized.
Federal companies within the U.S. have till June sixth to exchange affected gadgets or implement defenses that scale back or remove the chance of an assault.
Actively exploited flaws
The vulnerability in Google Chrome, tracked as CVE-2024-4761, has been confirmed by the seller as actively exploited on Could thirteenth however no technical particulars is at the moment publicly out there.
It’s described as an out of bounds write vulnerability in Chrome’s V8 JavaScript engine that executes JS code within the browser and its severity ranking is excessive.
Two days after disclosing CVE-2024-4761 Google introduced that one other vulnerability (CVE-2024-4947) in Chrome’s V8 engine has been exploited within the wild, however CISA has but so as to add it to the KEV catalog.
CISA can be warning {that a} ten-year previous vulnerability impacting D-Hyperlink DIR-600 routers continues to be being exploited. The flaw is recognized as CVE-2014-100005 and is a cross-site request forgery (CSRF) situation.
It permits attackers to hijack administrator authentication requests to the machine’s internet admin panel, create their very own admin accounts, change the configuration, and take management of the machine.
Though D-Hyperlink DIR-600 routers have reached end-of-life (EOL) 4 years earlier than being found, the seller launched a repair on the time in firmware model 2.17b02 together with a safety bulletin containing mitigation suggestions.
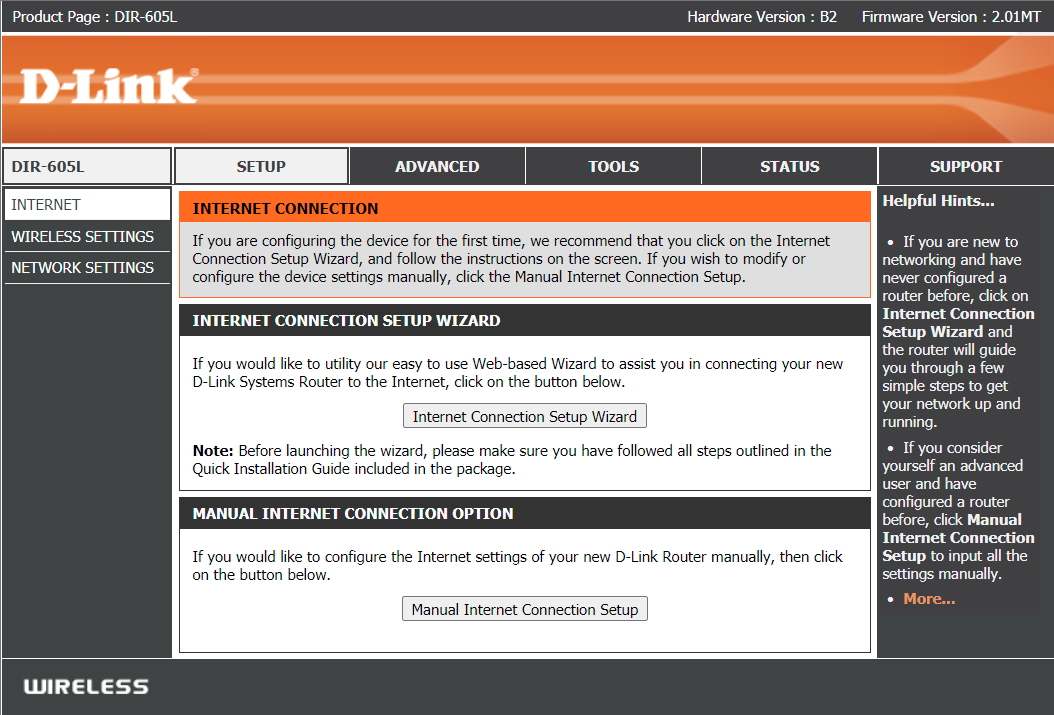
One other bug affecting D-Hyperlink merchandise has additionally been added not too long ago to the KEV catalog. It’s recognized as CVE-2021-40655 and impacts D-Hyperlink DIR-605 routers which have been out of assist since 2015.
A proof-of-concept exploit for the flaw was launched on GitHub in 2021. It demonstrated that an attacker might seize the admin’s username and password through a specifically crafted request despatched to the /getcfg.php web page with out authentication.
Supply: Github
CISA has not offered any background details about the 2 D-Hyperlink flaws and it’s unclear who exploited them or when the company recorded the assaults.
Older vulnerabilities are usually leveraged by botnet malware that incorporate massive lists of exploitable safety points with no regard to the kind of machine or age of the difficulty.
Within the case of D-Hyperlink 600 and 605, it is suggested to exchange the machine with newer fashions that the seller nonetheless helps with efficiency and safety updates.
