New cybersecurity analysis has discovered that command-line interface (CLI) instruments from Amazon Internet Providers (AWS) and Google Cloud can expose delicate credentials in construct logs, posing important dangers to organizations.
The vulnerability has been codenamed LeakyCLI by cloud safety agency Orca.
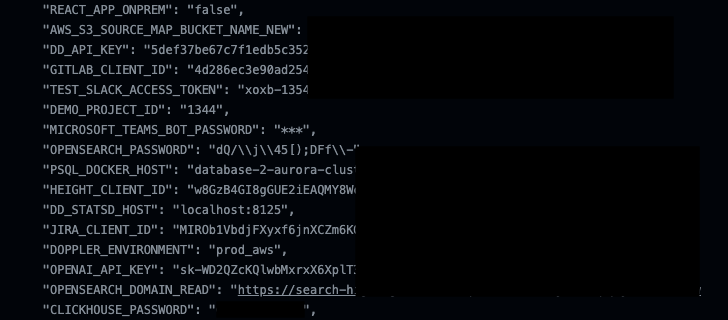
“Some commands on Azure CLI, AWS CLI, and Google Cloud CLI can expose sensitive information in the form of environment variables, which can be collected by adversaries when published by tools such as GitHub Actions,” safety researcher Roi Nisimi mentioned in a report shared with The Hacker Information.
Microsoft has since addressed the problem as a part of safety updates launched in November 2023, assigned it the CVE identifier CVE-2023-36052 (CVSS rating: 8.6).
The thought, in a nutshell, has to do with how the CLI instructions equivalent to might be used to indicate (pre-)outlined atmosphere variables and output to Steady Integration and Steady Deployment (CI/CD) logs. An inventory of such instructions spanning AWS and Google Cloud is beneath 0
- aws lambda get-function-configuration
- aws lambda get-function
- aws lambda update-function-configuration
- aws lambda update-function-code
- aws lambda publish-version
- gcloud capabilities deploy <func> –set-env-vars
- gcloud capabilities deploy <func> –update-env-vars
- gcloud capabilities deploy <func> –remove-env-vars
Orca mentioned it discovered a number of tasks on GitHub that inadvertently leaked entry tokens and different delicate knowledge through Github Actions, CircleCI, TravisCI, and Cloud Construct logs.
In contrast to Microsoft, nonetheless, each Amazon and Google contemplate this to be anticipated conduct, requiring that organizations take steps to keep away from storing secrets and techniques in atmosphere variables and as a substitute use a devoted secrets and techniques retailer service like AWS Secrets and techniques Supervisor or Google Cloud Secret Supervisor.
Google additionally recommends using the “–no-user-output-enabled” choice to suppress the printing of command output to plain output and normal error within the terminal.
“If bad actors get their hands on these environment variables, this could potentially lead to view sensitive information including credentials, such as passwords, user names, and keys, which could allow them to access any resources that the repository owners can,” Nisimi mentioned.
“CLI commands are by default assumed to be running in a secure environment, but coupled with CI/CD pipelines, they may pose a security threat.”