The Iranian state-backed hacking outfit known as APT42 is making use of enhanced social engineering schemes to infiltrate goal networks and cloud environments.
Targets of the assault embrace Western and Center Jap NGOs, media organizations, academia, authorized companies and activists, Google Cloud subsidiary Mandiant stated in a report printed final week.
“APT42 was observed posing as journalists and event organizers to build trust with their victims through ongoing correspondence, and to deliver invitations to conferences or legitimate documents,” the corporate stated.
“These social engineering schemes enabled APT42 to harvest credentials and use them to gain initial access to cloud environments. Subsequently, the threat actor covertly exfiltrated data of strategic interest to Iran, while relying on built-in features and open-source tools to avoid detection.”
APT42 (aka Damselfly and UNC788), first documented by the corporate in September 2022, is an Iranian state-sponsored cyber espionage group tasked with conducting info assortment and surveillance operations towards people and organizations of strategic curiosity to the Iranian authorities.
It is assessed to be a subset of one other notorious risk group tracked as APT35, which can be identified by numerous names CALANQUE, CharmingCypress, Charming Kitten, ITG18, Mint Sandstorm (previously Phosphorus), Newscaster, TA453, and Yellow Garuda.
Each the teams are affiliated with Iran’s Islamic Revolutionary Guard Corps (IRGC), however function with a special set of objectives.
Whereas Charming Kitten focuses extra on long-term, malware-intensive operations focusing on organizations and firms within the U.S. and Center East to steal knowledge. APT42, in distinction, targets particular people and organizations that the regime has its eye on for the aim of home politics, international coverage, and regime stability.
Earlier this January, Microsoft attributed the Charming Kitten actor to phishing campaigns focusing on high-profile people engaged on Center Jap affairs at universities and analysis organizations in Belgium, France, Gaza, Israel, the U.Ok., and the U.S. since November 2023.
Assaults mounted by the group are identified to contain intensive credential harvesting operations to collect Microsoft, Yahoo, and Google Credentials through spear-phishing emails containing malicious hyperlinks to lure paperwork that redirect the recipients to a pretend login web page.
In these campaigns, the adversary has been noticed sending emails from domains typosquatting the unique entities and masquerading as information retailers; official companies like Dropbox, Google Meet, LinkedIn, and YouTube; and mailer daemons and URL shortening instruments.
The credential-grabbing assaults are complemented by knowledge exfiltration actions focusing on the victims’ public cloud infrastructure to pay money for paperwork which are of curiosity to Iran, however solely after gaining their belief – one thing Charming Kitten is well-versed at.
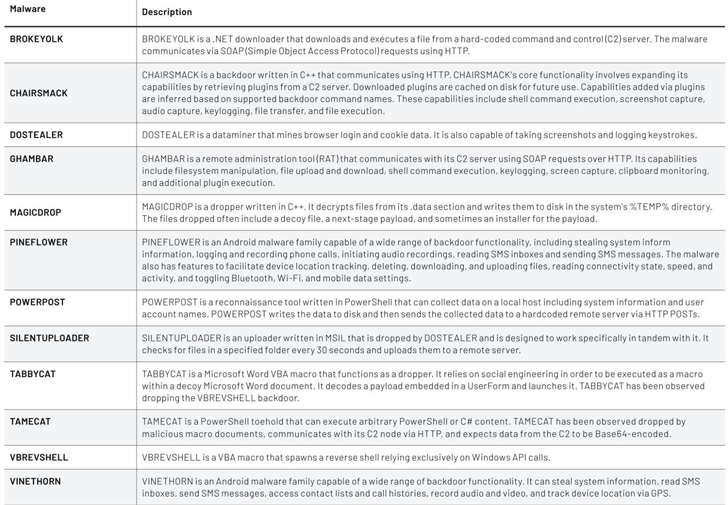 |
| Recognized malware households related to APT42 |
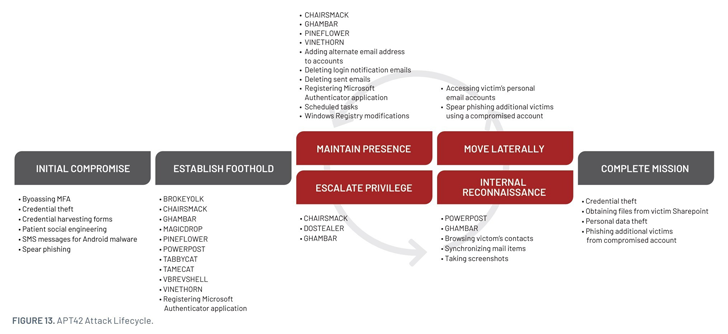
“These operations began with enhanced social engineering schemes to gain the initial access to victim networks, often involving ongoing trust-building correspondence with the victim,” Mandiant stated.
“Only then the desired credentials are acquired and multi-factor authentication (MFA) is bypassed, by serving a cloned website to capture the MFA token (which failed) and later by sending MFA push notifications to the victim (which succeeded).”
In an effort to cowl up its tracks and mix in, the adversary has been discovered counting on publicly out there instruments, exfiltrating information to a OneDrive account masquerading because the sufferer’s group, and using VPN and anonymized infrastructure to work together with the compromised atmosphere.
Additionally utilized by APT42 are two customized backdoors that act as a leaping level to deploy further malware or to manually execute instructions on the gadget –
- NICECURL (aka BASICSTAR) – A backdoor written in VBScript that may obtain further modules to be executed, together with knowledge mining and arbitrary command execution
- TAMECAT – A PowerShell toehold that may execute arbitrary PowerShell or C# content material
It is value noting that NICECURL was beforehand dissected by risk intelligence and incident response agency Volexity in February 2024 in reference to a collection of cyber assaults geared toward Center East coverage specialists between September and October 2023.
“APT42 has remained relatively focused on intelligence collection and targeting similar victimology, despite the Israel-Hamas war that has led other Iran-nexus actors to adapt by conducting disruptive, destructive, and hack-and-leak activities,” Mandiant concluded.
“The methods deployed by APT42 leave a minimal footprint and might make the detection and mitigation of their activities more challenging for network defenders.”