Cybersecurity researchers have found a focused operation in opposition to Ukraine that has been discovered leveraging a virtually seven-year-old flaw in Microsoft Workplace to ship Cobalt Strike on compromised techniques.
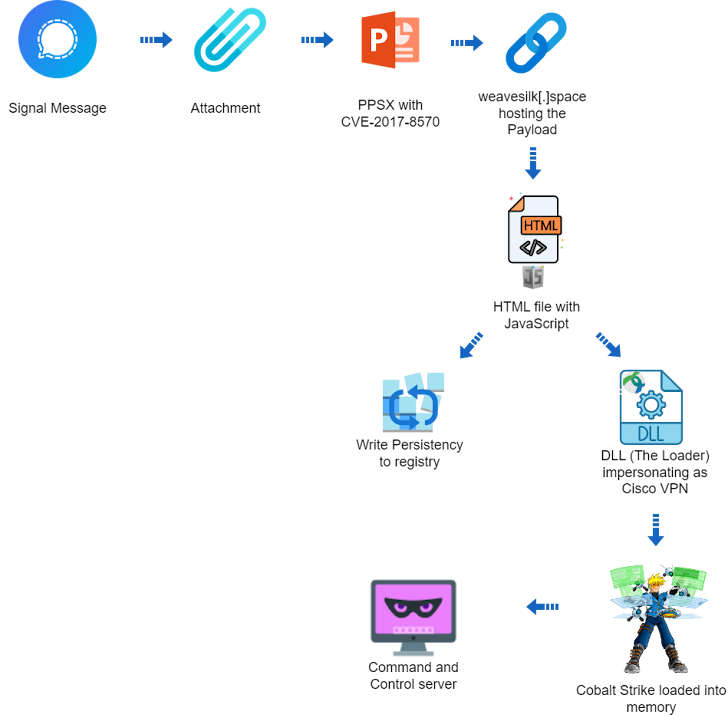
The assault chain, which befell on the finish of 2023 based on Deep Intuition, employs a PowerPoint slideshow file (“signal-2023-12-20-160512.ppsx”) as the place to begin, with the filename implying that it might have been shared by way of the Sign immediate messaging app.
That having stated, there isn’t any precise proof to point that the PPSX file was distributed on this method, despite the fact that the Laptop Emergency Response Group of Ukraine (CERT-UA) has uncovered two completely different campaigns which have used the messaging app as a malware supply vector up to now.
Simply final week, the company disclosed that Ukrainian armed forces are being more and more focused by the UAC-0184 group by way of messaging and relationship platforms to serve malware like HijackLoader (aka GHOSTPULSE and SHADOWLADDER), XWorm, and Remcos RAT, in addition to open-source applications equivalent to sigtop and tusc to exfiltrate knowledge from computer systems.
“The PPSX (PowerPoint slideshow) file appears to be an old instruction manual of the U.S. Army for mine clearing blades (MCB) for tanks,” safety researcher Ivan Kosarev stated. “The PPSX file includes a remote relationship to an external OLE object.”
This includes the exploitation of CVE-2017-8570 (CVSS rating: 7.8), a now-patched distant code execution bug in Workplace that would enable an attacker to carry out arbitrary actions upon convincing a sufferer to open a specifically crafted file, to load a distant script hosted on weavesilk[.]house.
The closely obfuscated script subsequently launches an HTML file containing JavaScript code, which, in flip, units up persistence on the host by way of Home windows Registry and drops a next-stage payload that impersonates the Cisco AnyConnect VPN consumer.
The payload features a dynamic-link library (DLL) that finally injects a cracked Cobalt Strike Beacon, a official pen-testing instrument, immediately into system reminiscence and awaits for additional directions from a command-and-control (C2) server (“petapixel[.]fun”).
The DLL additionally packs in options to verify if it is being executed in a digital machine and evade detection by safety software program.
Deep Intuition stated it might neither hyperlink the assaults to a particular menace actor or group nor exclude the opportunity of a pink teaming train. Additionally unclear is the precise finish aim of the intrusion.
“The lure contained military-related content, suggesting it was targeting military personnel,” Kosarev stated.
“But the domain names weavesilk[.]space and petapixel[.]fun are disguised as an obscure generative art site (weavesilk[.]com) and a popular photography site (petapixel[.]com). These are unrelated, and it’s a bit puzzling why an attacker would use these specifically to fool military personnel.”
The disclosure comes as CERT-UA revealed that about 20 power, water, and heating suppliers in Ukraine have been focused by a Russian state-sponsored group known as UAC-0133, a sub-cluster inside Sandworm (aka APT44, FROZENBARENTS, Seashell Blizzard, UAC-0002, and Voodoo Bear), which is accountable for a bulk of all of the disruptive and damaging operations in opposition to the nation.
The assaults, which aimed to sabotage crucial operations, contain the usage of malware like Kapeka (aka ICYWELL, KnuckleTouch, QUEUESEED, and wrongsens) and its Linux variant BIASBOAT, in addition to GOSSIPFLOW and LOADGRIP.
Whereas GOSSIPFLOW is a Golang-based SOCKS5 proxy, LOADGRIP is an ELF binary written in C that is used to load BIASBOAT on compromised Linux hosts.
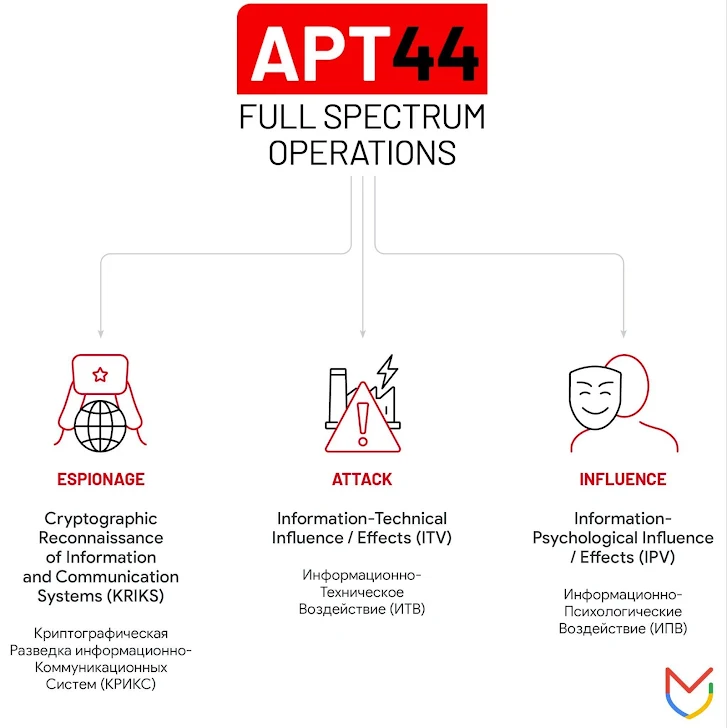
Sandworm is a prolific and extremely adaptive menace group linked to Unit 74455 inside the Predominant Directorate of the Normal Workers of the Armed Forces of the Russian Federation (GRU). It is identified to be energetic since a minimum of 2009, with the adversary additionally tied to 3 hack-and-leak hacktivist personas equivalent to XakNet Group, CyberArmyofRussia_Reborn, and Solntsepek.
“Sponsored by Russian military intelligence, APT44 is a dynamic and operationally mature threat actor that is actively engaged in the full spectrum of espionage, attack, and influence operations,” Mandiant stated, describing the superior persistent menace (APT) as engaged in a multi-pronged effort to assist Russia acquire a wartime benefit since January 2022.
“APT44 operations are global in scope and mirror Russia’s wide ranging national interests and ambitions. Patterns of activity over time indicate that APT44 is tasked with a range of different strategic priorities and is highly likely seen by the Kremlin as a flexible instrument of power capable of serving both enduring and emerging intelligence requirements.”