A passkey is a particular authentication technique that can be utilized as generally as a password however to supply extra safety. Passkeys differ from passwords as they mix non-public and public cryptographic keys to authenticate customers, whereas a password depends on a particular variety of characters.
In line with Google, essentially the most instant advantages of passkeys are that they’re phishing-resistant and spare individuals the headache of remembering numbers and particular characters in passwords.
As passwordless authentication continues to evolve — in response to phishing-related dangers — think about using passkeys to implement an added layer of safety to guard your on-line accounts and information.
This text will outline passkey expertise, discover the way it works, and focus on the added safety advantages of utilizing a passkey.
What’s a passkey?
A passkey refers to a code or a collection of characters used to realize entry to a secured system, gadget, community, or service. Passkeys are sometimes used together with usernames or consumer IDs to create two-factor authentication.
SEE: The best way to Create an Efficient Cybersecurity Consciousness Program (TechRepublic Premium)
After you’ve established a passkey, all you want to do is log in to finish the authentication course of, usually utilizing biometric information akin to a fingerprint or facial recognition. For many who make the most of a passkey, logging in turns into a easy, practically computerized course of; for malicious actors, it turns into practically inconceivable.
The implementation of passkeys is extremely adaptable since they could be configured to be cloud-synced or hardware-bound, contingent on the consumer’s decisions relating to the actual software, service, or gadget.
How do passkeys work?
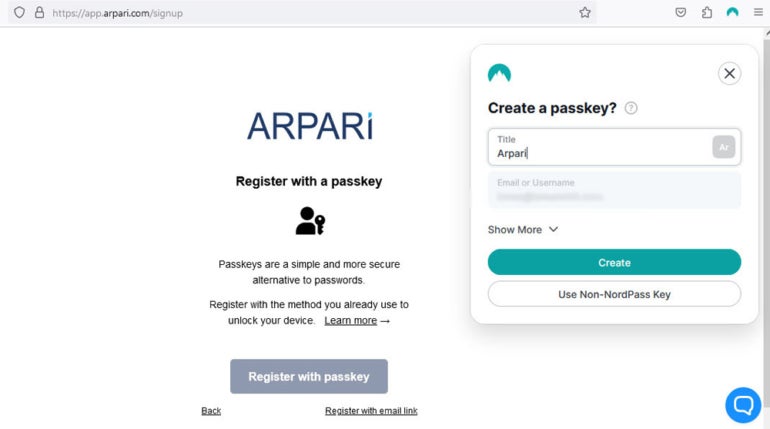
When logging in for the primary time, a consumer who needs to entry an app or web site with passkey expertise — akin to NordPass — might be requested to generate an unique passkey. This passkey, which might be required for authentication sooner or later, will be accessed utilizing both biometrics or private PINs based mostly on the consumer’s choice and the capabilities of their most well-liked gadget.
Determine A
Throughout this stage, two mathematically linked cryptographic keys are generated: a public key that stays with the web site, service, or software however is related to the account, and a non-public key that stays on the consumer’s {hardware} or cloud account.
How do you sign up with a passkey as an alternative of a password?
Passkey authentication is completed within the background, making login on the consumer’s finish seamless — with simply the clicking of a button.
Determine B
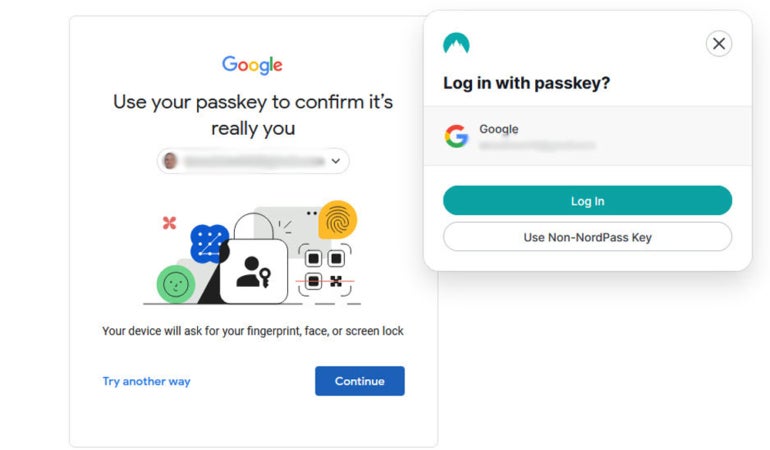
The service or software will ship a randomly generated “challenge” to the consumer’s gadget throughout logins, which the consumer should react to by signing in with the non-public key.
SEE: Passkey Adoption Is Accelerating in APAC — Aside from Australia (TechRepublic)
The app or web site can verify the legitimacy of the non-public key by using the corresponding public key to substantiate the response. Entry is allowed, and authentication is validated if the consumer’s verified signature hooked up to the problem’s response agrees with the unique randomly generated problem; if not, entry is denied.
How are passkeys completely different from passwords?
Essentially the most important variations between passkeys and passwords embody:
- Passwords will be illicitly obtained by means of brute-force hacking, social engineering, and information breaches, whereas passkeys are tougher (although not inconceivable) to steal. Hackers would wish to bodily steal your gadget or breach your cloud account and guess your PIN or discover a strategy to bypass your biometric authenticator.
- Safe password utilization requires customers to generate and bear in mind many complicated credentials or make use of a password supervisor, which has its personal challenges and dangers. Passkeys mechanically authenticate customers with their gadget’s unlock mechanisms, making them a lot less complicated and extra handy to make use of.
- Passwords can be utilized throughout any gadget with none extra setup, however passkeys are normally sure to particular {hardware}. A cloud-based passkey answer may go throughout a number of units, however customers needs to be conscious that their non-public keys might be saved on another person’s servers as an alternative of domestically.
What are the advantages of utilizing a passkey?
- Distinctive logins: A password is reused each time you log in to a selected account, which implies any malicious actor who will get their arms on it would have unfettered entry. Passkeys, however, use cryptographic key pair expertise to create distinctive authentication credentials for each login, giving hackers nothing to “guess” or steal. Passkeys are immune to brute drive assaults and social engineering strategies like phishing, plus they’ll’t be uncovered in a knowledge breach.
- Added safety layer: Passkeys use your gadget’s authenticator, akin to a biometric login or PIN code, as a form of built-in 2FA that protects your account. Whether or not your non-public secret’s saved domestically in your gadget or within the cloud, a would-be hacker would wish to authenticate along with your gadget earlier than having access to it and compromising your account.
- Person comfort: Passkeys don’t should be memorized or periodically modified, and logging in with them requires a single button press, offering a way more streamlined expertise than passwords. And, as I simply talked about, they embody 2FA to raised shield accounts, however they don’t require customers to supply secondary authentication for every particular person login — when you’ve logged into your gadget, that authentication is utilized to each account you entry that session.
What units are appropriate with passkeys?
Many units from the most well-liked tech producers are appropriate with passkeys. Passkey expertise was developed in keeping with W3C and FIDO Alliance requirements to assist in compatibility, and the massive three gadget producers (Apple, Google, and Microsoft), in addition to all main internet browsers, already assist it.
Can passkeys be shared?
The implementation of passkey expertise continues to be growing, however some firms have talked about the potential for credential sharing amongst customers — so long as the precise passkeys are saved protected within the cloud and out of the arms of potential hackers. Since sharing account entry with household, mates, and coworkers is a quite simple and fast course of, this function could enhance the general consumer expertise. Nevertheless, it’s nonetheless unclear how this perform will be securely managed in a enterprise setting.
SEE: The best way to Use Google’s Titan Safety Keys With Passkey Assist (TechRepublic)
One other essential issue to think about is whether or not companies ought to grow to be much more depending on cloud suppliers and quit much more possession and management over credential administration, given {that a} breach of these events’ information would, indisputably, have disastrous penalties.
{Hardware}-bound passkeys, versus cloud-based passkeys, are saved on safety keys, bodily {hardware} authenticators, or specialised {hardware} built-in into laptops and desktops. Which means that the passkey is neither transferable nor duplicated. {Hardware}-bound passkeys will be another for organizations wanting to forestall workers from copying or sharing keys throughout units.
Are passkeys safer than passwords?
Typically talking, passkeys are safer than passwords. Nevertheless, their safety will depend on numerous components, together with the power of the cryptographic strategies used to encrypt private and non-private keys, the safety of the gadget’s authenticator, and the trustworthiness of the passkey answer supplier.
SEE: Practically 10 Billion Passwords Leaked in Greatest Compilation of All Time (TechRepublic)
Customers can take steps to make passkeys safer, nonetheless. For instance, passkeys use your gadget credentials as a second type of authentication, so utilizing biometric login as an alternative of a PIN can increase the safety of your non-public key. Minimizing cookie assortment and periodically clearing cached credentials are additionally good practices for bettering general internet safety. It’s additionally important to enrich passkeys with different safety instruments and controls, akin to encrypted laborious drives, gadget malware safety, and firewalls.
Can a passkey be hacked?
Sure, passkeys will be hacked, nevertheless it’s rather more troublesome than stealing a password. As I’ve described above, passkeys are protected by a number of layers of safety, together with native gadget authentication and powerful encryption. Merely buying the non-public key just isn’t sufficient as a result of, even with cloud-based passkey options, you want to authenticate with the native gadget earlier than you’ll be able to entry any on-line accounts.
Will passkeys substitute passwords and password managers?
For my part, passkeys will finally substitute passwords and password managers, although the transition is presently nonetheless at first phases. As passkey expertise improves and extra companies undertake it, we’ll doubtless see passwords section out even amongst dwelling customers.
What’s the way forward for passkeys in expertise?
Proper now, many of the improvements in passkey expertise are — appropriately, in my view — centered on options, that are extra handy for builders and companies to make use of within the hopes of driving adoption.
For instance, proper now, passkeys created in a single ecosystem don’t simply work with others. So, if a consumer creates a passkey utilizing their iPhone, it’s troublesome, if not inconceivable, to make use of the identical passkey on a Home windows laptop computer or to switch all of their passkeys from one surroundings to a different.
This limitation, nonetheless, solely actually applies to the environment-native passkey instruments that include newer Apple, Home windows, and Android units. As extra third-party passkey suppliers enter the market, the usual is starting to shift towards cross-platform assist and simpler portability to enhance the shopper expertise.