Cybersecurity researchers have found an intricate multi-stage assault that leverages invoice-themed phishing decoys to ship a variety of malware akin to Venom RAT, Remcos RAT, XWorm, NanoCore RAT, and a stealer that targets crypto wallets.
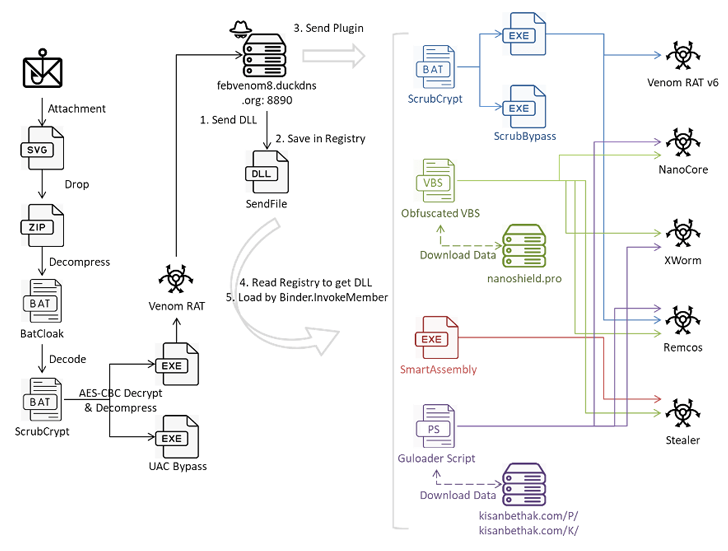
The e-mail messages include Scalable Vector Graphics (SVG) file attachments that, when clicked, activate the an infection sequence, Fortinet FortiGuard Labs mentioned in a technical report.
The modus operandi is notable for the usage of the BatCloak malware obfuscation engine and ScrubCrypt to ship the malware within the type of obfuscated batch scripts.
BatCloak, provided on the market to different risk actors since late 2022, has its foundations in one other device known as Jlaive. Its major function is to load a next-stage payload in a fashion that circumvents conventional detection mechanisms.
ScrubCrypt, a crypter that was first documented by Fortinet in March 2023 in reference to a cryptojacking marketing campaign orchestrated by the 8220 Gang, is assessed to be one of many iterations of BatCloak, in response to analysis from Pattern Micro final 12 months.
Within the newest marketing campaign analyzed by the cybersecurity agency, the SVG file serves as a conduit to drop a ZIP archive that incorporates a batch script doubtless created utilizing BatCloak, which then unpacks the ScrubCrypt batch file to finally execute Venom RAT, however not earlier than organising persistence on the host and taking steps to bypass AMSI and ETW protections.
A fork of Quasar RAT, Venom RAT permits attackers to grab management of the compromised programs, collect delicate info, and execute instructions obtained from a command-and-control (C2) server.
“While Venom RAT’s primary program may appear straightforward, it maintains communication channels with the C2 server to acquire additional plugins for various activities,” safety researcher Cara Lin mentioned. This consists of Venom RAT v6.0.3 with keylogger capabilities, NanoCore RAT, XWorm, and Remcos RAT.
“This [Remcos RAT] plugin was distributed from VenomRAT’s C2 using three methods: an obfuscated VBS script named ‘remcos.vbs,’ ScrubCrypt, and Guloader PowerShell,” Lin added.
Additionally delivered utilizing the plugin system is a stealer that gathers details about the system and exfiltrates information from folders related to wallets and purposes like Atomic Pockets, Electrum, Ethereum, Exodus, Jaxx Liberty (retired as of March 2023), Zcash, Foxmail, and Telegram to a distant server.
“This analysis reveals a sophisticated attack leveraging multiple layers of obfuscation and evasion techniques to distribute and execute VenomRAT via ScrubCrypt,” Lin mentioned.
“The attackers employ a variety of methods, including phishing emails with malicious attachments, obfuscated script files, and Guloader PowerShell, to infiltrate and compromise victim systems. Furthermore, deploying plugins through different payloads highlights the versatility and adaptability of the attack campaign.”